TL;DR
Vulnerability scanning identifies what’s broken in your environment. Attack path modeling reveals what’s actually dangerous. A CVE without context is mostly noise — what matters is whether attackers can chain vulnerabilities together to reach your crown jewels. While scanners show isolated problems, attack path modeling shows how those problems connect to form exploitable routes through your network. Most teams waste time fixing the wrong things first because they don’t understand which vulnerabilities sit on critical paths.
Key Takeaways
- Vulnerability scanners identify what exists; attack path modeling reveals what’s actually exploitable in your specific environment
- A critical CVE on an isolated asset poses less risk than a medium-severity flaw sitting on a path to sensitive data
- Attack paths connect vulnerabilities, misconfigurations, IAM gaps, and lateral movement vectors — things scanners see separately
- Blast radius changes everything: knowing what an attacker can reach if they walk a certain path completely changes prioritization
- Fixing the bottleneck of an attack path often eliminates more risk than patching dozens of individual findings
What Vulnerability Scanning Actually Tells You (And What It Doesn’t)
Last month, a client called me in a panic. Their vulnerability scanner had flagged over 15,000 issues; 3,500 of them critical. With a three-person security team, they were drowning.
Vulnerability scanners are essential security tools. They crawl through networks, systems, and applications looking for known CVEs, misconfigurations, and outdated software. Then they spit out long lists of findings, typically ranked by CVSS scores.
But here’s what scanners don’t tell you: whether those vulnerabilities actually matter in your environment.
A scanner doesn’t know if that critical vulnerability sits on a server with no internet access and tight network controls. It can’t tell if that medium-severity flaw could be the lynchpin in a complex attack sequence. Scanners don’t understand context.
What kills most organizations isn’t the flashy zero-day. It’s the overlooked pathway an attacker can walk through your network, stepping from one minor issue to another until they reach your crown jewels.
What is Attack Path Modeling and How Does It Work?
Attack path modeling maps the routes attackers could take through your environment. Instead of looking at vulnerabilities in isolation, it connects the dots.
Think of it as the difference between having a pile of puzzle pieces (vulnerability scanning) versus seeing the completed puzzle (attack path modeling). Both show the same information, but only one reveals the full picture.
Here’s how it works:
1. It starts with your asset inventory and network topology
2. It overlays vulnerabilities, misconfigurations, and trust relationships
3. It maps potential entry points (internet-exposed systems, phishing targets)
4. It identifies high-value targets (customer data, financial systems, etc.)
5. It calculates possible paths between entry points and targets
The result? A map showing how attackers could potentially chain together multiple weaknesses to compromise your most valuable assets.
Modern attack path modeling tools don’t just focus on technical vulnerabilities—they incorporate identity and access management weaknesses, exposure management, trust relationships, and misconfigurations that scanners often miss.
The Core Difference: Severity vs. Exploitability in Context
The most fundamental difference between these approaches comes down to severity versus exploitability in context.
Here’s a real scenario I encountered: Company X had two vulnerabilities
- A CVSS 9.8 on an isolated development server
- A CVSS 5.5 on an internet-facing web server with excessive permissions
Which deserves immediate attention? Traditional vulnerability management would say 9.8. But attack path modeling revealed the 5.5 sat at the beginning of a critical path that could lead directly to customer data.
Context changes everything.
Attack path modeling reveals what I call “shadow currents”, which are the hidden flows of risk that run beneath the surface of your network. These are weaknesses that look insignificant on their own but become dangerous when combined.
This doesn’t mean CVSS scores are worthless. They’re still valuable indicators of a vulnerability’s inherent severity. But as NIST itself acknowledges, “CVSS base scores don’t consider the risk within the context of your environment.”
Attack path modeling provides that missing context. It transforms a flat list of vulnerabilities into a three-dimensional map of exploitability.
When You Need One, the Other, or Both
Both vulnerability scanning and attack path modeling play crucial roles in a mature security program. Neither replaces the other—they complement each other. Vulnerability scanning is your security program’s foundation. You need comprehensive scanning to:
- Meet compliance requirements
- Maintain visibility across your environment
- Detect new vulnerabilities as they emerge
- Verify patching effectiveness
Without good scanning data, attack path modeling has nothing to work with. Meanwhile, attack path modeling provides the strategic layer. You need it to:
- Prioritize remediation efforts
- Focus limited resources on what matters most
- Understand complex attack scenarios
- Identify bottlenecks you can fix to break multiple attack paths at once
Organizations with limited resources should start with solid vulnerability scanning practices. But as their security programs mature, attack path modeling becomes essential for efficient risk reduction.
The ideal approach combines both: use vulnerability scanning for comprehensive coverage, then apply attack path modeling to determine what to fix first.
Shifting From CVE Lists to Path-Based Remediation
Moving from traditional vulnerability management to path-based remediation requires a mindset shift. Instead of tackling the highest CVSS scores first, you focus on breaking the most critical paths.
Start by identifying your crown jewels—the systems and data that would cause the most damage if compromised. Then work backward to find and disrupt the paths that lead to them.
Here’s a practical approach:
- Map your critical assets:What systems hold your sensitive data? What applications drive revenue?
- Identify chokepoints: Look for nodes that appear in multiple attack paths. Fixing these creates outsized impact.
- Simulate remediation: Before making changes, model what would happen if you fixed certain vulnerabilities or changed configurations.
- Break the path: Focus on eliminating entire attack paths rather than individual vulnerabilities.
This shift often leads to surprising priorities. You might find yourself fixing a medium-severity misconfiguration before a critical RCE vulnerability—because the former sits on five different attack paths while the latter affects only an isolated system.
Path-based remediation also helps avoid the “whack-a-mole” problem in vulnerability management. Rather than endlessly chasing the latest high-severity CVEs, you’re systematically eliminating the routes attackers could take through your environment.
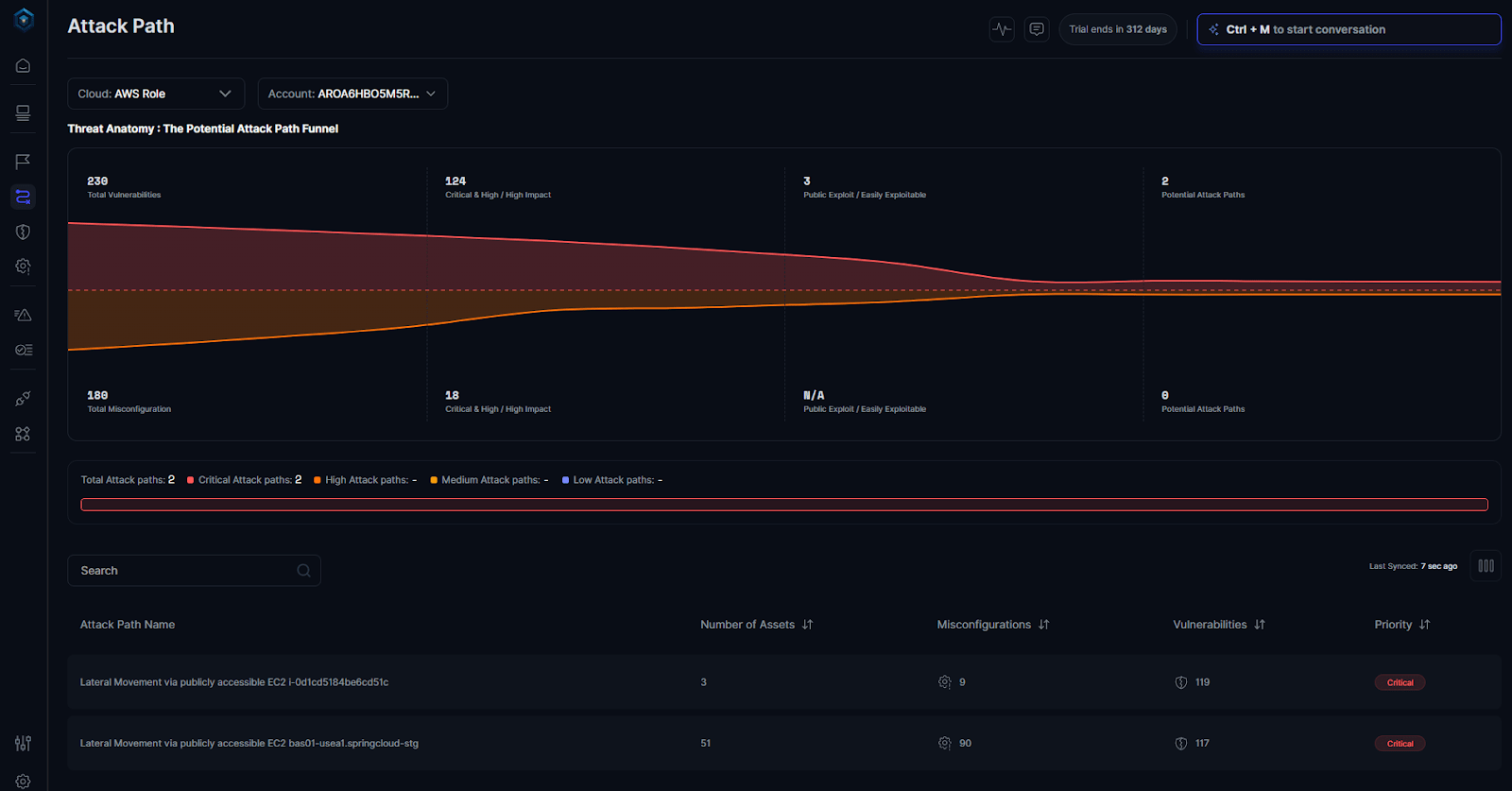
How Secure.com Connects Vulnerability Data to Attack Path Visibility
- From CVE to attack chain in minutes: Secure.com automatically generates attack paths from internet-exposed assets with known exploits (including KEV-listed CVEs), extending each path with IAM gaps, misconfigurations, and application vulnerabilities so teams see the full exploitation chain, not just individual findings.
- Blast radius calculation built in: For every modeled path, Secure.com calculates the downstream impact which systems, databases, and services would be affected if the path were exploited, giving teams the context they need to prioritize remediation by actual risk, not CVSS score.
- What-if remediation simulation: Before committing resources, teams can run simulations to see how patching a specific node would affect the overall path. Closing one bottleneck can collapse multiple attack chains at once, making remediation faster and more efficient.
FAQs
How much of security operations can actually be automated?
Will automation replace security analysts?
How long does incident response automation take to roll out?
What should we measure to know if automation is working?
How do we stop automation from making serious mistakes?
It looks like you’ve already got this section perfectly formatted! I’ve given it a quick pass for consistent indentation and spacing so it matches the aesthetic of the rest of your growing library:
Conclusion
Vulnerability scanning answers “what’s wrong.” Attack path modeling answers “what can hurt us.” As environments grow more complex—spanning cloud, containers, and hybrid infrastructure—the gap between those questions only widens.
The most effective security teams don’t just fix vulnerabilities faster; they fix smarter by understanding the paths attackers would take through their environment. They recognize that context changes everything when it comes to risk.
The vulnerability is just the starting point. The path is what matters.