Detection
- Ingest SIEM / EDR / IAM / Cloud
- Normalize events (OCSF)
- Enrich with threat intel

Detect, triage, investigate, and respond—fast. Every action stays human-approved and auditable.
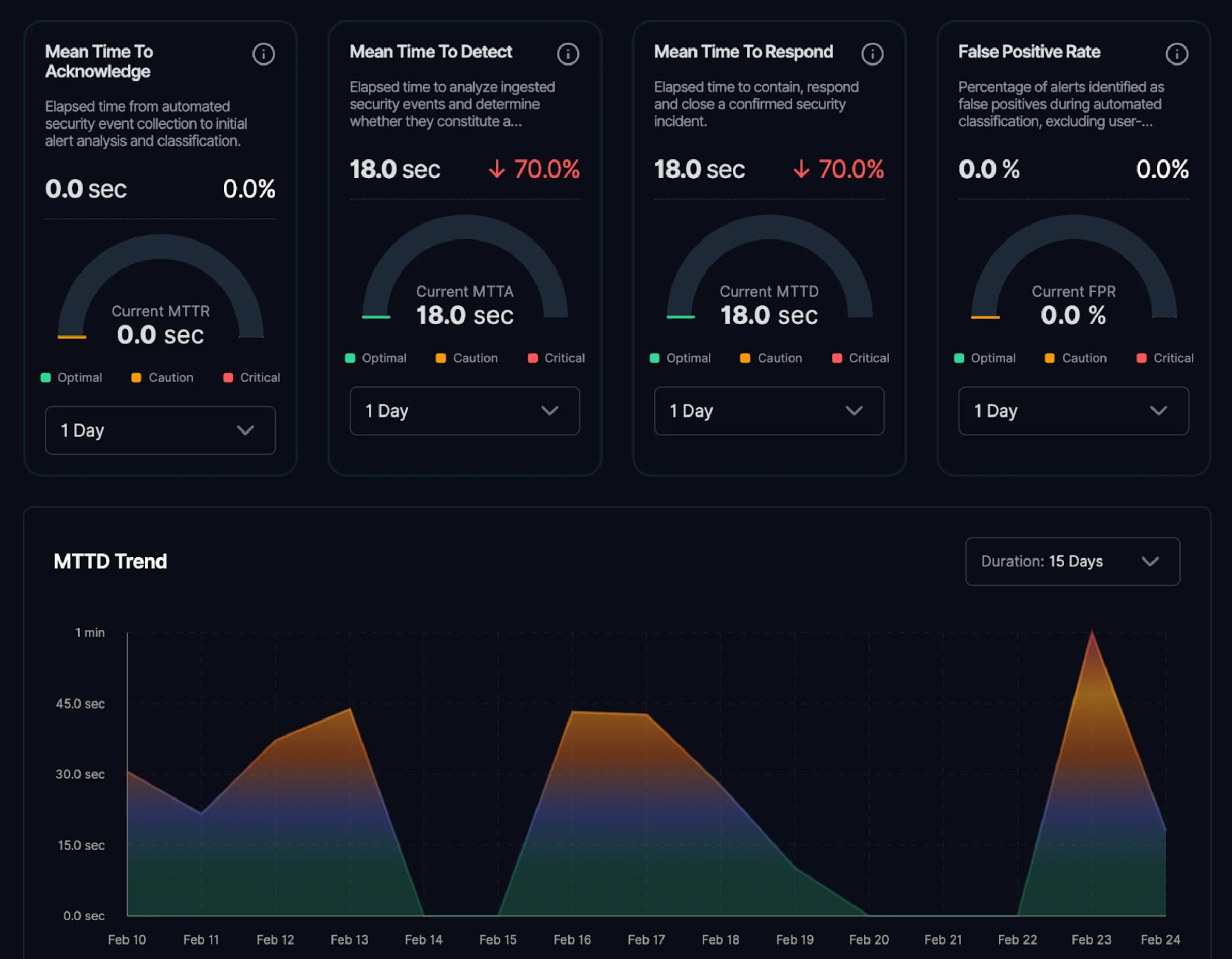
See measurable improvements in detection, response, and triage times that transform how your security operations team works.
Automated signal normalization, threat-intel enrichment, and MITRE correlation surface real incidents in minutes — not hours.
Pre-approved playbooks execute containment instantly, with human-in-loop approvals and full case tracking.
Context-aware prioritization combines asset criticality, exploitability (KEV), identity risk, and blast radius — eliminating alert noise at scale.
AI SOC tools summarize alerts. Your SOC Teammate runs case end to end.
Four core capabilities that transform how your SOC detects, triages, investigates, and responds to threats.
Ingest signals from SIEM, EDR, IAM, cloud, and email security
Normalize and enrich events with threat intelligence
Surface high-fidelity, actionable detections
Map activity to MITRE ATT&CK
See attacker intent - not raw telemetry
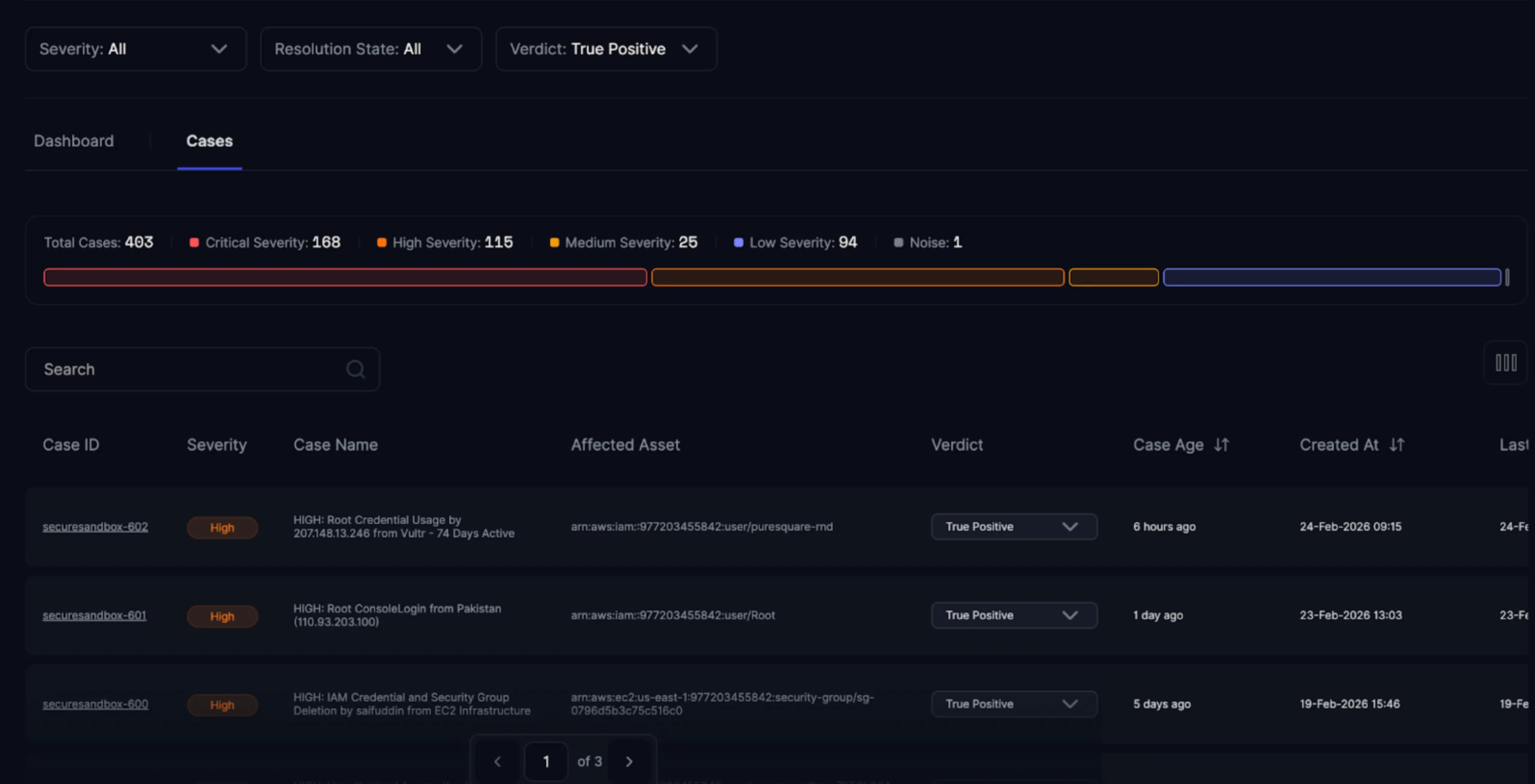
Auto-triage alerts into structured cases
Assign clear ownership and enforce SLAs
Correlate findings with asset criticality and exploitability
Add identity context to prioritize by business impact
Reduce noise so every meaningful signal becomes actionable work
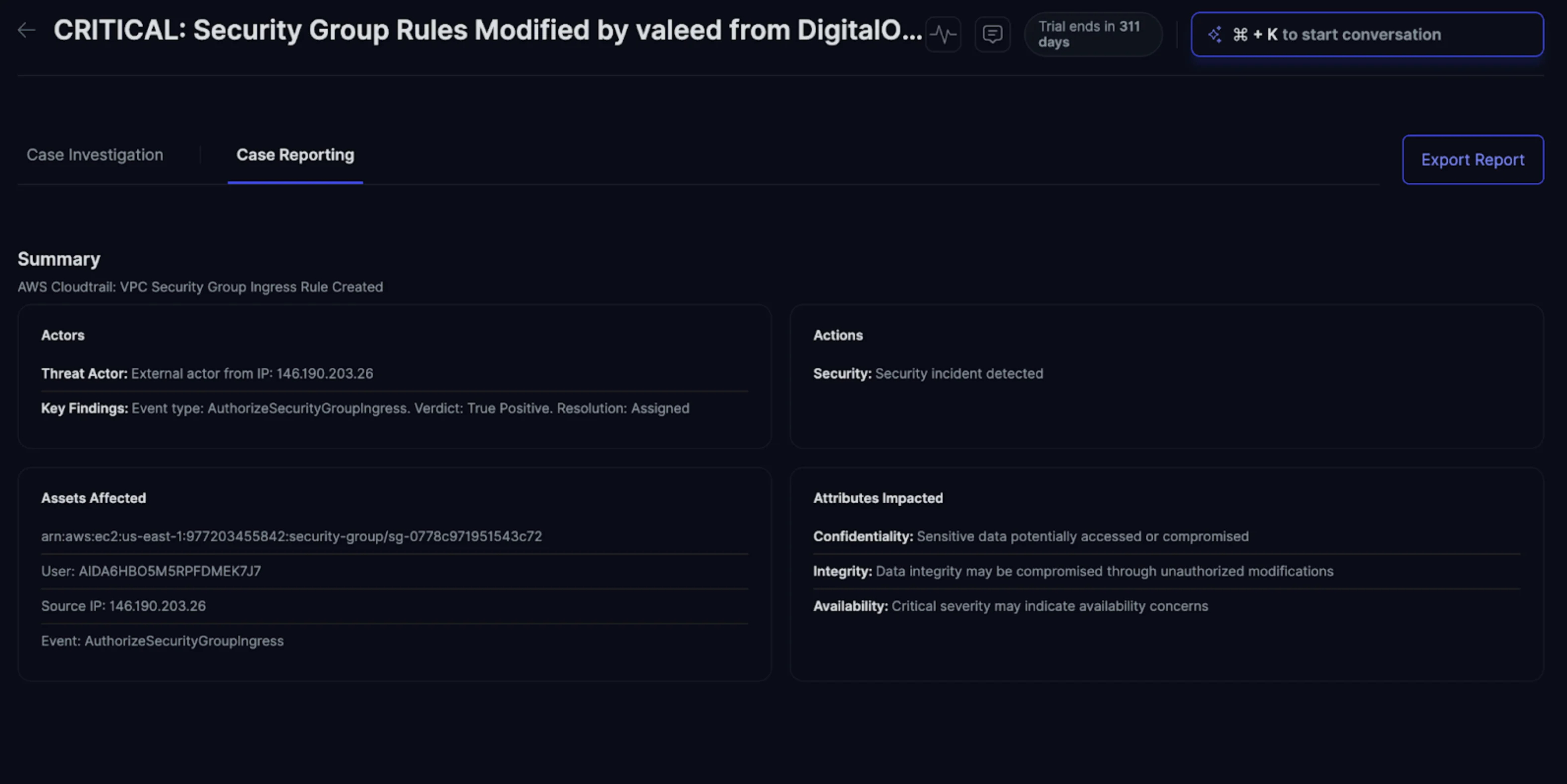
Pull full context directly into the case
Identify crown-jewel assets and blast radius
Map KEV/CVE relevance and misconfiguration exposure
Detect identity misuse and service impact
Link evidence, timelines, and decisions in one workflow
Trigger pre-approved playbooks for containment and response
Isolate hosts and disable compromised accounts
Notify asset owners and create tickets automatically
Keep high-impact actions human-in-the-loop
Log every step with full traceability
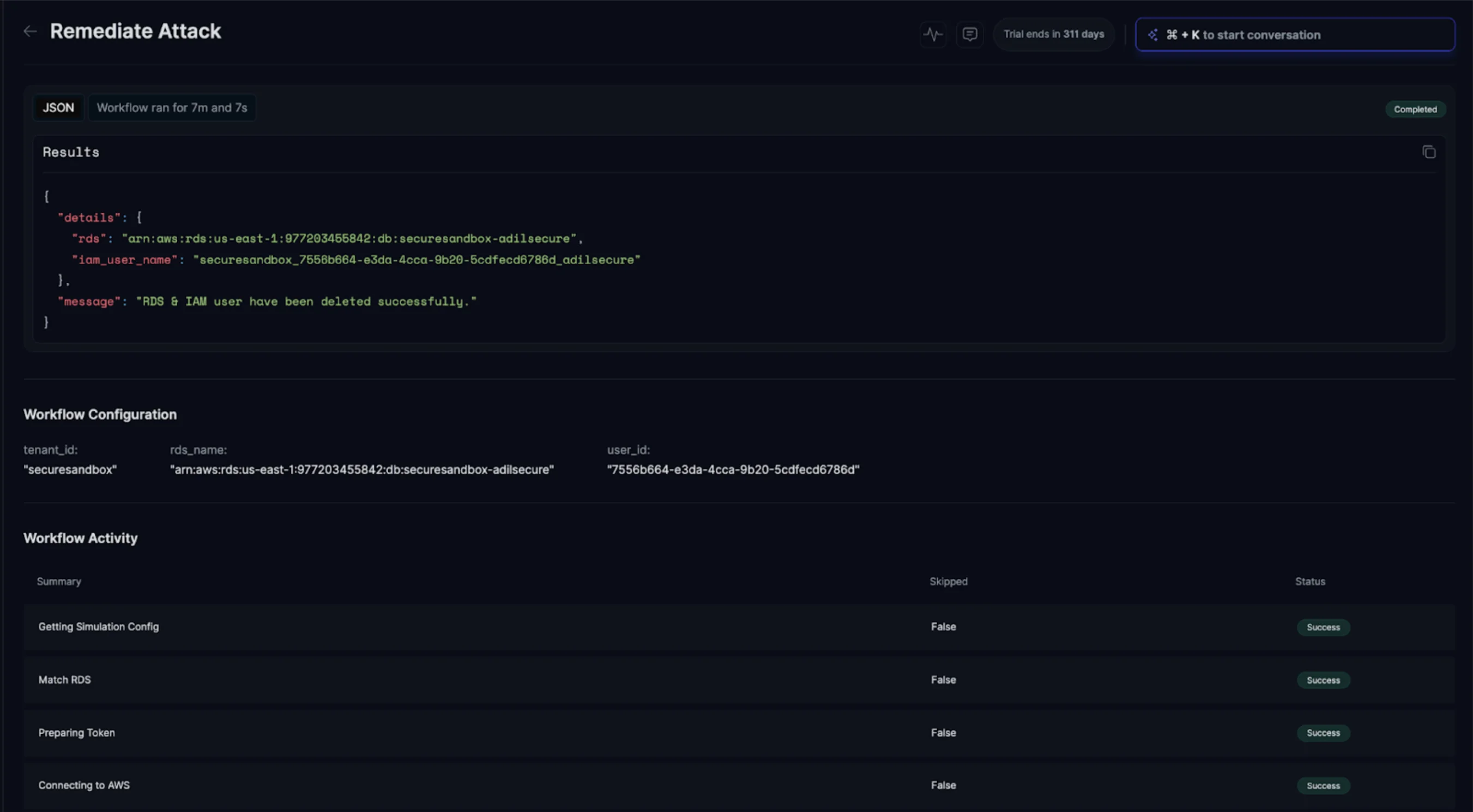
Trigger pre-approved playbooks for containment and response—host isolation, account disablement, owner notifications, and ticket creation. High-impact actions stay human-in-the-loop. Every step is logged, reversible, and traceable back to the case for audit and review.