TL;DR
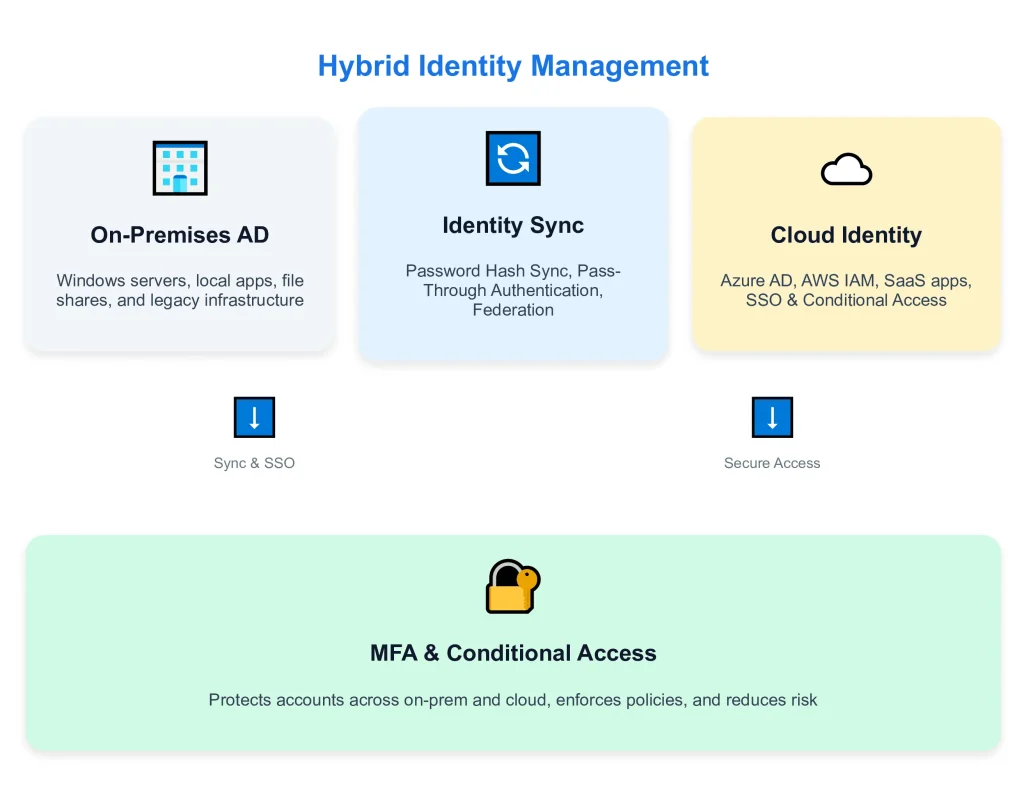
Organizations adopt hybrid identity to maintain legacy investments while accessing cloud services, but face challenges including synchronization conflicts, security complexity, and credential sprawl—modern approaches use password hash sync or pass-through authentication with tools like Azure AD Connect to balance security with user experience.
Key Takeaways
- Hybrid identity bridging two worlds: It connects an on-premises Active Directory with cloud-based identity providers for more unified access management.
- Three sync methods are available: Password Hash Sync is the most common; Pass-Through Authentication is considered the most Secure.com, and Federation is seen as the most complex.
- Single sign-on is the goal: Users identify themselves once to gain access to both on-premises and cloud resources without having to log in multiple times.
- Security is complicated by this: Every integration point creates potential vulnerabilities so MFA and conditional access are mandatory.
- Migration is gradual, too: Most organizations spend between two and five years in a hybrid state before possibly moving entirely to cloud identity management.
Introduction
Your developers need AWS access, the sales team is always in Salesforce, and Finance is buried in those on-site ERP systems. In the meantime, IT is juggling 3,000 user accounts across Active Directory, Azure AD, AWS IAM, and Google Workspace—all with passwords expiring at different times and access requests that take too long to process.
This is the modern hybrid identity challenge. According to Gartner, a huge 85% of enterprises work in hybrid or multi-cloud environments. Yet only 23% have unified identity management for all their systems.
The result? A study by Verizon found that 60% of data breaches involved stolen credentials– often exploiting gaps between on-premises and cloud identity systems.
Hybrid identity management solves this problem by synchronizing identities between your existing infrastructure and cloud services. This enables single sign-on as well as centralized access control. However, implementing it can create new security challenges meaning deployment requires careful planning.
What is Hybrid Identity Management?
Hybrid identity management synchronizes user identities, authentication credentials, and access permissions between on-premises directory services (typically Active Directory) and cloud-based identity providers (Azure AD, AWS IAM, Google Workspace, Okta).
Why Organizations Adopt Hybrid Identity Management
- Keeping hold of their existing Active Directory setups even as they start using cloud services
- Making sure the move to the cloud can happen bit by bit with no impact on how users get their work done
- Offering single sign-on (SSO) for those who still want apps in the office plus ones that are purely cloud-based
- Centralizing those all-important user accounts: making them when required and removing them when no longer needed
- Meeting compliance requirements by having centralized control over access
What are the Components of Hybrid Identity Management?
On-Premises Directory Service
- User authentication for on-premises applications
- Group Policy enforcement for Windows devices
- LDAP authentication for legacy enterprise applications
- File share access permissions
Cloud Identity Provider
- Single sign-on for Office 365 and Salesforce, as well as thousands of other SaaS applications
- Easy access to cloud platforms like Azure, AWS, and GCP
- Manage mobile devices and set policies that adapt based on conditions
- Use current authentication methods such as SAML, OAuth, and OpenID Connect
Identity Synchronization Engine
- Runs on-premises server (typically domain-joined Windows Server)
- Polls Active Directory for changes every 30 minutes (configurable)
- Pushes user account updates to cloud identity provider
- Handles password synchronization using one of three methods (detailed below)
Authentication Method
- Most common method (used by 70%+ of Azure AD hybrid deployments)
- Syncs hashed passwords from AD to Azure AD
- Users authenticate directly against Azure AD using synchronized credentials
- Fastest user experience, simplest to implement
- Security consideration: Password hashes exist in both locations
Single Sign-On (SSO)
- User logs into Windows laptop (authenticates against on-premises AD)
- Opens web browser, navigates to Office 365
- Browser automatically sends Kerberos ticket or SAML assertion
- Azure AD validates identity without password re-entry
- User gains access without second login
Multi-Factor Authentication (MFA)
- Cloud application access (enforced by Azure AD, Okta, etc.)
- VPN connections to on-premises resources
- Admin account access (should require MFA everywhere)
- Conditional access scenarios (new device, unusual location)
Conditional Access Policies
- Require MFA from untrusted locations
- Block access from non-compliant devices
- Enforce password change if leaked credentials detected
- Restrict administrative access to specific IP ranges
- Require managed devices for accessing sensitive data
What are Some Hybrid Identity Examples?
Example 1: Enterprise with Office 365 Migration
Scenario: A business with 5,000 employees shifts its email from an in-house Exchange server to Microsoft’s cloud-based Office 365. Nonetheless, the firm continues to use Active Directory on its local network– mainly for authenticating Windows logins.
Hybrid Identity Setup:
- Azure AD Connect syncs 5,000 user accounts from AD to Azure AD
- Password Hash Sync chosen for simplicity and disaster recovery
- Seamless SSO enabled for domain-joined Windows devices
- MFA enforced for all cloud access except from corporate network
- On-premises users access Office 365 without password prompts
Example 2: Multi-Cloud SaaS Company
Scenario: Tech startup uses Google Workspace for email, AWS for infrastructure, Okta for app management, and maintains small AD for file servers.
Hybrid Identity Setup:
- Okta connects to on-premises AD via the LDAP connector
- Google Workspace syncs users from Okta via SAML federation
- AWS IAM integrated with Okta for SSO to the AWS Console
- Salesforce, Slack, Zoom, and GitHub all authenticate via Okta
- AD remains an authoritative source for user creation/deletion
Example 3: Healthcare Organization with Compliance Requirements
Scenario: Hospital maintains an on-premises electronic health record (EHR) system requiring Active Directory. Adopts Office 365 for email, but must prevent PHI exposure in the cloud.
Hybrid Identity Setup:
- Azure AD Connect with Pass-Through Authentication (passwords never sync to cloud)
- Conditional access blocks Office 365 access from personal devices
- MFA required for any access outside the hospital network
- On-premises AD remains the sole authentication source
- Information Rights Management prevents email forwarding of sensitive data
Example 4: Merger and Acquisition Integration
Scenario: Company acquires competitor. The acquired company uses different AD forests. Both need access to shared systems while maintaining separate identities.
Hybrid Identity Setup:
- Two separate Azure AD Connect instances sync from both AD forests
- Azure AD B2B collaboration enables cross-tenant access
- Acquired company users invited as guests in the parent company Azure AD
- Parent company maintains a separate forest trust for on-premises resource access
- Gradual account migration planned over 18 months
Example 5: Retail Chain with Store Locations
Scenario: National retailer with 500 stores. Each store has point-of-sale systems requiring local AD. Corporate offices use cloud services.
Hybrid Identity Setup:
- Regional AD domain controllers in each geographic area
- Azure AD Connect syncs corporate users only (not store POS accounts)
- Store employees use local AD credentials for POS systems
- Corporate employees use synchronized Azure AD for Office 365, Salesforce
- Separate identity tiers prevent credential compromise in stores from affecting the corporate
What are the Use Cases of Hybrid Identity Management?
Cloud Migration Without Service Disruption
- Maintain Active Directory for legacy apps during migration
- Gradually move workloads to the cloud while preserving authentication
- Users experience no disruption—SSO works across both environments
- IT migrates services at a manageable pace (months or years)
Single Sign-On Across Hybrid Environment
- One credential set works everywhere (on-premises and cloud)
- Seamless SSO eliminates repeated login prompts
- Users authenticate once at device login, and access everything
- Password resets are synced automatically across environments
Centralized User Lifecycle Management
- Create a user once in Active Directory (or HR system)
- Automated provisioning creates accounts in all connected systems
- Single disable action revokes access everywhere
- Deprovisioning workflows ensure no orphaned accounts
Regulatory Compliance and Data Sovereignty
- Pass-Through Authentication keeps passwords exclusively on-premises
- Satisfies the requirements that authentication must occur in a controlled data center
- Audit logs from Azure AD provide compliance evidence
- Conditional access enforces compliance policies before granting access
Mergers and Acquisitions Integration
- Azure AD B2B lets the acquired company access parent resources as guests
- Both companies maintain separate AD while enabling collaboration
- Gradual account migration over 18 months without disrupting business
- Decommission acquired AD after migration completes
Supporting Remote and Mobile Workforce
Cloud-based authentication works from anywhere (no VPN required)
- Conditional access enforces MFA for untrusted locations
- Seamless SSO on company laptops (trusted devices)
- Device compliance checks prevent unmanaged device access
Multi-Cloud and SaaS Application Access
- Azure AD (or Okta) becomes central identity provider
- SAML/OAuth federation to AWS, Salesforce, Workday, ServiceNow
- One identity in AD provisions access to all platforms
- Centralized deprovisioning removes access from all systems
Supporting Legacy Applications During Modernization
- Maintain AD for legacy app authentication
- Hybrid identity enables modern cloud services alongside
- Gradual application of modernization without forcing “works with your existing stack.”
- When the legacy app is finally retired, disable AD sync gradually
What are the Challenges of Hybrid Cloud Identity Management?
Expanded Attack Surface and Security Complexity
- Attackers use common passwords for synced accounts, trying both on-premises and cloud systems.
- If the Azure AD Connect server is compromised, the attacker can obtain password hashes.
- Password Hash Synchronization (PHS) means password hashes are stored in both Active Directory and Azure AD— presenting more opportunities for attack.
- Without proper security measures, there is a potential risk of interception for synchronization traffic.
Synchronization Conflicts & Data Consistency
- Group membership is changed in both places during the sync window.
- When a user is deleted from AD but the sync is delayed— they can still access cloud resources.
- And there are attribute mapping conflicts too (AD stores phones as 10 digits but Azure AD needs an international format).
Password Expiration & Policy Misalignment
- AD requires 12-character passwords—Azure AD wants just 8 (users thus create weak cloud passwords).
- AD blocks using the last 24 passwords; Azure AD blocks the last 10 (seen as inconsistent enforcement).
- MFA is mandatory in the cloud but not on-premises (reflecting an inconsistent security stance).
- Account lockout thresholds vary too much (AD locks after 5 tries, Azure AD after 10).
Complexity in Troubleshooting Access Issues
- There are too many systems to examine: AD, Azure AD, sync agents, and applications.
- It’s challenging to correlate logs across these different platforms.
- Plus, changes don’t take effect immediately; they can take up to half an hour.
- Cached credentials also disguise the real situation– and each component has its own separate admin portal!
Limited Visibility & Monitoring
- You can’t see the entire authentication path from user login right through to application access.
- Sync errors are hidden away in event logs on the on-premise server.
- Azure AD sign-in logs don’t reveal on-premise authentication details.
- Conditional access decisions aren’t visible in real-time dashboards.
- There’s no alert system if syncing stops or starts malfunctioning either!
Dependency on On-Premises Infrastructure
- The Azure AD Connect server must be operational at all times (because syncing halts if it goes offline).
- Domain controllers have to be available too (PTA needs them for authentication).
- There must be network connectivity between the premises and cloud.
- For reliable syncing a VPN or ExpressRoute is required (internet outages will disrupt syncing).
Compliance & Audit Challenges
- Audit logs end up divided between these two: AD event logs and Azure AD logs.
- Forget a single unified view of user access across different environments.
- Proving who had access when is like doing a complicated jigsaw puzzle with info from multiple systems.
- Retention periods used to be another obstacle (AD logs typically last 90 days; Azure AD is configurable).
- The export and correlation process really gets into the nitty-gritty!
Securing Hybrid Identity Beyond Synchronization
Constant vigilance is required in identity management. A few examples include:
- Detecting permissions that stray too far from a least-privilege model
- Identifying accounts left behind by ex-employees
- Spotting gaps in multi-factor authentication particularly for users whose identities are synchronized between on-premises directories and cloud services.
This is an area where traditional synchronization tools provide no assistance—although Secure.com may be able to help fill the gap.
The platform scans for accounts in Active Directory, Azure AD, AWS IAM, and more than 200 connected apps, then uses this information to identify potential security issues.
Example
Disabled users who can log in to cloud services, admin accounts without multi-factor authentication, or privilege escalation paths that would allow an attacker to elevate their privileges if they had stolen credentials.
Instead of having to visit six different admin portals, security teams see unified dashboards showing overall identity security across the hybrid infrastructure.
These include automated remediation workflows that route fixes to the appropriate owners, transforming hybrid identity from a compliance headache into an auditable foundation under control.
FAQs
What’s the difference between hybrid identity and federated identity?
How long does it take to implement hybrid identity management?
Can you have hybrid identity without Active Directory?
Is hybrid identity more secure than cloud-only identity?
Conclusion
Hybrid identity management is what helps connect older systems located on company premises with newer cloud services. This lets organizations start using the cloud at their own speed without messing up how things run. But here’s the thing: hybrid identity also brings some tricky security issues, makes monitoring harder, and adds extra work that all needs careful handling.
Organizations have to make sure MFA gets used everywhere, put conditional access policies in place, keep a close eye on sync health all the time, and get ready for a full move to the cloud someday rather than thinking the hybrid setup is going to stay as it is forever.
The real aim? Getting hold of those great security features from cloud identity like passwordless sign-in options, smart risk-based conditional access, and automated threat detection—things you just can’t take full advantage of with hybrid setups.
Ready to eliminate identity blind spots? Secure.com’s Digital Security Teammates provide continuous visibility across hybrid environments, automated risk scoring for identity exposures, and integrated workflows for access management.



