No Camera, No Problem: How WiFi Became the World’s Sneakiest Spy Tool
The router in your home has always been a passive device. It moves data. It doesn’t watch you. That assumption just got a lot harder to defend.
A new open-source tool called RuView (built by developer Reuven Cohen and now publicly available on GitHub) can reconstruct full-body human poses through walls in real time, using nothing but standard WiFi signals. No cameras. No special hardware. Just the radio signals already bouncing around your space.
RuView hit number one on GitHub trending on February 27, 2026, picking up over 4,500 stars in a single day. That kind of attention is rare and telling.
What Happened?
RuView implements WiFi DensePose, a sensing technique originally pioneered by Carnegie Mellon University, as a practical, low-cost edge system that reconstructs full-body human poses through walls.
The underlying science isn’t new. Carnegie Mellon researchers used three $30 WiFi routers and three aligned receivers to map WiFi signal phase and amplitude onto human body coordinates. What’s new is that this research has now been packaged into a tool anyone can download and run in 30 seconds using Docker.
At its core, the system exploits Channel State Information (CSI); metadata that WiFi hardware already collects. When a human body moves within a wireless environment, it distorts signal paths across dozens of subcarriers. RuView captures these disturbances, extracts amplitude and phase variations, and feeds them through a deep learning architecture to produce a real-time reconstruction of 24 body surface regions.
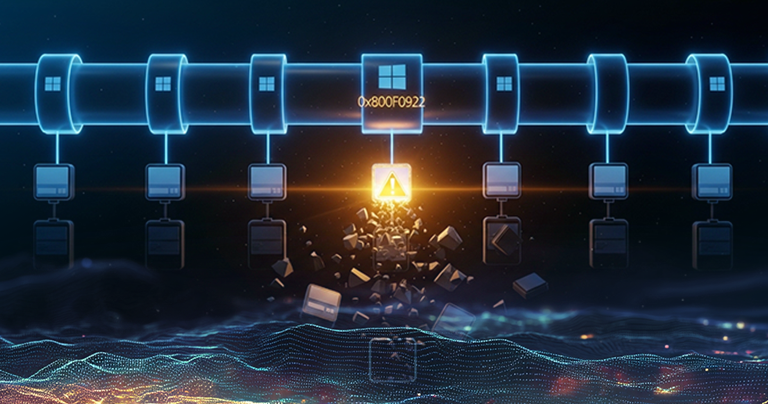
The system achieves roughly 87% accuracy, and the Rust implementation delivers sub-50ms latency at 30 frames per second.
It runs on inexpensive ESP32 hardware — as low as $1 per node — entirely offline, with no cloud dependency.
What’s the Impact?
The threat scenario is blunt. A bad actor plants a $5 ESP32 node near a WiFi access point, deploys RuView via Docker, and begins silently mapping occupants’ movements, routines, and biometric vitals through walls. No physical access to the target space is required. No visible hardware. Nothing to find on a camera sweep.
There’s also a deeper problem: existing privacy law wasn’t written for this. Unlike cameras, which are regulated under GDPR, CCPA, and physical installation laws, passive WiFi CSI sensing is invisible and requires no physical access to the target environment. Nobody has to ask permission. Nobody has to be caught on film.
Researchers have noted that state-level actors likely already have this capability — “I don’t know that people are actually doing that, but I’m sure we are capable,” said one WiFi sensing expert.
How to Avoid This
There’s no single clean fix — but these steps reduce your exposure:
For individuals: Check your network for unknown devices, especially low-cost microcontrollers (ESP32, Raspberry Pi Zero) that have no obvious reason to be on your network segment.
For organizations: Security teams should treat passive RF sensing as an emerging physical-layer threat. Mitigations include RF shielding in sensitive facilities and monitoring for rogue ESP32-class devices on network segments.
For high-risk environments: Faraday shielding in meeting rooms, server rooms, and executive offices is worth revisiting. What used to feel like overkill now has a concrete use case.
Push for policy: The regulatory gap is real. CSI-based tracking has no legal framework addressing it yet — and the technology is already deployable at consumer prices. That gap won’t close on its own.
The router in your office isn’t just a networking device anymore. For anyone without protections in place, it’s a sensor.