TL;DR
Remediation permanently fixes a vulnerability at its root. Mitigation reduces the risk when an immediate fix isn’t possible — use both to stay protected.
Key Takeaways
- Remediation eliminates a vulnerability entirely by fixing its root cause — through patching, code changes, or system upgrades.
- Mitigation lowers the risk of exploitation when a full fix isn’t available yet — using controls like network segmentation or access restrictions.
- In 2024, a record-breaking 40,009 CVEs were published — no team can remediate everything at once.
- CISA recommends remediating critical vulnerabilities within 15 days, but over 60% of known exploited vulnerabilities remain unremediated past their designated deadlines.
- A combined remediation + mitigation strategy is not optional — it’s the baseline for a mature security program.
Introduction
A hospital discovers a critical flaw in its patient records software. The vendor patch won’t be ready for two weeks. Should the security team wait — or act now?
This is where the remediation vs. mitigation question becomes real. Understanding the difference helps your team make faster, smarter decisions when every hour of exposure counts.
What is Vulnerability Remediation?
Remediation is the permanent fix. It removes the vulnerability at its source so it can no longer be exploited.
Remediation is the process of fully resolving a vulnerability or threat by addressing its root cause. Organizations aim to eliminate the issue entirely, ensuring that the vulnerability cannot be exploited again in the future.
Common remediation actions include:
- Patching software — applying the vendor-released fix for a known CVE
- Upgrading systems — replacing outdated versions with secure alternatives
- Reconfiguring settings — closing gaps caused by misconfiguration
- Rewriting insecure code — fixing the flaw at the application level
- Decommissioning end-of-life assets — removing systems that can no longer be secured
When to prioritize remediation:
Remediation is the right call when a patch is available, the system can tolerate downtime, and the vulnerability poses a high or critical risk. CISA recommends that high-risk vulnerabilities be remediated within 30 days, and critical vulnerabilities within 15 days of detection.
The challenge:
The average time to remediate a vulnerability has increased to 270 days across many organizations — creating a critical window where mitigation becomes essential. That gap is exactly where mitigation comes in.
What is Vulnerability Mitigation?
Mitigation is the temporary shield. It doesn’t fix the flaw — it makes it harder to exploit while a fix is being prepared.
Mitigation reduces the likelihood or impact when a full fix isn’t immediately viable — through approaches like segmentation, temporary feature disablement, or access restrictions. Often, teams mitigate now and remediate later when the patch, maintenance window, or vendor support is available.
Common mitigation strategies include:
- Network segmentation — isolating vulnerable systems to limit the blast radius
- Access control restrictions — using MFA and role-based access control (RBAC) to limit exposure
- Intrusion prevention systems (IPS) — blocking known attack patterns in real time
- Disabling vulnerable features — turning off non-essential functions until a patch is ready
- Enhanced monitoring — increasing logging and alerting around at-risk assets
When mitigation makes sense:
Not all vulnerabilities can be remediated immediately. A patch may not be available yet, an important operational system may be vulnerable but intolerable for downtime, or out-of-date systems may exist that aren’t directly accessible by malicious actors. In each case, mitigation is the responsible move.
The risk of mitigation alone:
Mitigation is not a finish line. A mitigated vulnerability remains exploitable. If compensating controls fail or attackers discover an alternate attack path, the risk resurfaces — often without warning. It must always be paired with a remediation plan.
Vulnerability Remediation vs. Mitigation: What are the Differences?
The short version: remediation closes the door. Mitigation locks it while you find the key. Here is a side-by-side breakdown:
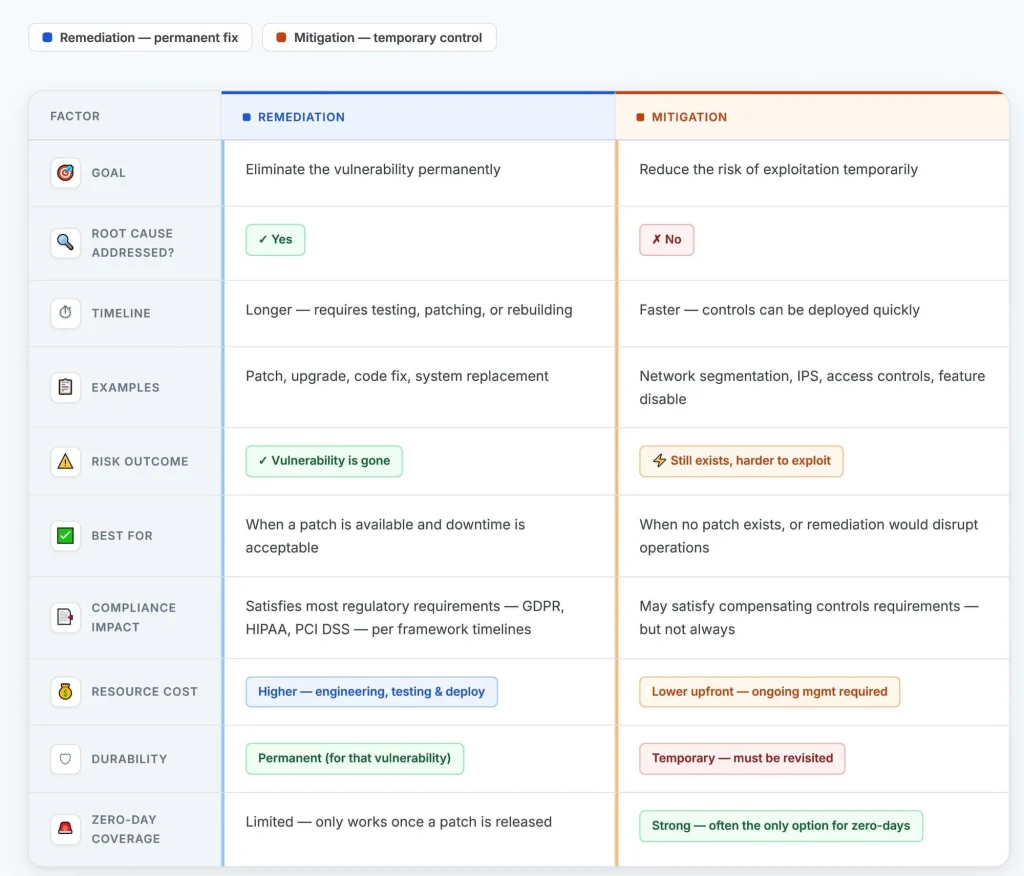
The bottom line: Understanding when to prioritize remediation vs. mitigation is crucial for effective cybersecurity program management. While remediation provides a more permanent solution, mitigation offers a way to maintain security even when a full resolution is not possible.
Neither strategy works alone. The strongest security programs run them together — mitigating to buy time, remediating to close the gap for good.
How Secure.com Can Help in Vulnerability Remediation and Mitigation
Secure.com unifies remediation and mitigation workflows in a single platform — enabling your team to prioritize based on real business risk, automate response actions, and close security gaps faster with less manual effort.
Risk-Based Prioritization
- Ranks vulnerabilities by actual business impact — combining CVSS scores with asset criticality, exploitability, and threat intelligence
- Helps teams focus remediation effort where it matters most — instead of chasing every CVE equally
- Reduces alert fatigue by surfacing what’s truly dangerous
Automated Remediation Workflows
- Triggers remediation actions based on predefined policies — with human approval required for high-impact changes
- Integrates with ticketing systems (like ServiceNow and Jira) to assign and track fixes
- Speeds up patch deployment across large, distributed environments
- Reduces the gap between vulnerability discovery and resolution
Attack Path Modeling
- Maps multi-hop attack paths showing how adversaries could chain vulnerabilities, misconfigurations
- Identifies weaknesses to move laterally from initial compromise to critical assets
- Guides mitigation decisions when full remediation isn’t yet possible
- Helps teams visualize real-world risk — not just theoretical severity scores
Application Security
- Integrates with application security tools to identify code-level vulnerabilities in CI/CD pipelines before production deployment
- Connects dev teams with security teams around shared remediation goals
- Integrates with SAST, DAST, and IAST tools to provide visibility across the entire development lifecycle
- Reduces the time between vulnerability discovery and developer action
Conclusion
Remediation and mitigation are not competing strategies — they’re two halves of a complete security program. Remediation closes vulnerabilities for good. Mitigation protects you while you get there.
The real risk is treating one as optional. Combining them is important because mitigation offers immediate risk reduction while remediation works on permanent fixes. Together, they help reduce overall risk exposure and build a more resilient security posture.
With the right platform behind your team, you can stop choosing between speed and thoroughness and start doing both.