TL;DR
Shadow IT, which refers to the use of apps, devices, and cloud services without authorization, creates huge security gaps that hackers take advantage of. To manage shadow IT, you’ll need automated detection but also crystal-clear policies plus much speedier delivery of services from your IT department– all working together to tackle the underlying causes.
Key Takeaways
- Around 30% of essential assets remain hidden, resulting in security weaknesses that can be exploited.
- The majority of shadow IT usage stems from individuals looking to improve efficiency rather than negative motives– although this still poses risks.
- New cloud services can be started in just a few minutes—meaning that quarterly checks miss the majority of shadow IT.
- Modern tools can find all your assets across cloud platforms, Saaas, and endpoints—no agents required.
- Paying for unused licenses, facing compliance fines and dealing with breach costs can run into millions each year.
Introduction
A big healthcare company, part of the Fortune 500, thought they had a good handle on their IT environment. IT had given the thumbs up to 42 cloud applications for staff use.
But when they ran automated asset discovery, they found 847 cloud apps actually being used and 805 totally unauthorized. Each one was a potential compliance violation, data breach risk, and security blind spot. This is shadow IT; unauthorized technology living inside your organization invisible to security teams until it’s too late.
According to Gartner, 30% of critical assets in most organizations go undiscovered creating attack surfaces that defenders can’t see but attackers can find. With cloud services launching in minutes and remote work pushing SaaS adoption higher, shadow IT isn’t just a problem anymore— it’s an epidemic breaking traditional security models.
Top Shadow IT Risks You Can’t Ignore
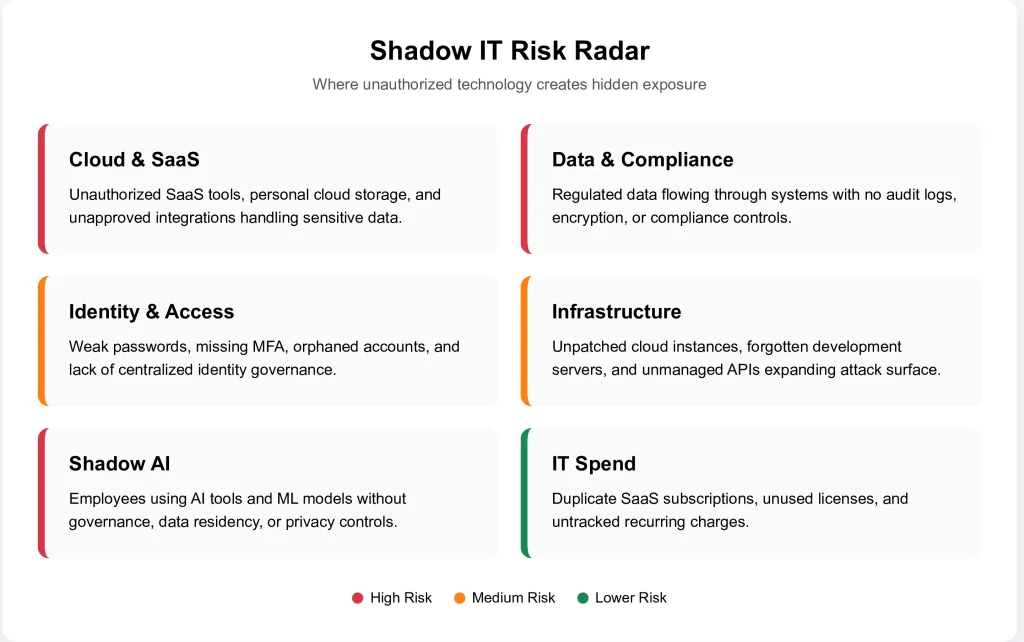
Data Breaches and Unauthorized Data Exposure
When employees share sensitive files on cloud storage that hasn’t been approved, use forbidden project management tools to collaborate, or stash data in personal accounts, they create direct routes for information to leak out. These services generally have zero encryption, poor access controls, and don’t integrate with your Data Loss Prevention (DLP) systems at all.
Real impact
Healthcare organizations face especially severe consequences here. Protected Health Information (PHI) that gets shared via unauthorized channels is a clear HIPAA violation—leading to regulatory fines plus the cost of breach notifications. The average data breach costs $4.45 million (IBM Cost of a Data Breach Report 2023), and breaches starting from unmanaged assets are tougher both to detect and contain.
Compliance Violations and Audit Failures
Regulatory frameworks such as HIPAA, PCI DSS, GDPR, SOC2, and ISO 27001 compel organizations to keep complete lists of systems that handle regulated data. But Shadow IT creates immediate compliance gaps because these rogue devices aren’t included in your official records.
Audit failure
- When auditors find out that data protected by regulation is moving across networks not authorized for its use, they flag it as an issue.
- Your organization could face fines if there are patterns like this.
Evidence collection impossible
- Compliance requires audit trails, access logs, and evidence of security controls.
- Shadow IT systems generate none of this documentation, making it impossible to prove compliance even if controls existed.
Unmanaged Vulnerabilities and Exploit Risks
Security teams can’t patch what they don’t even know exists. Many shadow IT apps operate older versions with identified weaknesses for this exact reason– they fall outside your vulnerability management scheme.
Attack surface expansion
- Each unauthorized application, cloud instance, or device expands your attack surface.
- Attackers use reconnaissance to find these assets and exploit them as initial access points. From there, they move laterally to your critical systems.
Zero visibility during incidents
- When a breach occurs through shadow IT, you have no logs, no monitoring data, and no forensic evidence to understand the attack chain or determine the scope of compromise.
Lack of Access Controls and Weak Authentication
Employees use weak passwords or reuse them across different systems; they also seldom activate MFA on unofficial tools. As a result, there’s no central control over identity management: no single sign-on (SSO) capability and therefore no means to enforce sensible password policies company-wide.
Orphaned access
- While identity lifecycle management typically revokes access to sanctioned systems during offboarding, shadow IT accounts remain active indefinitely—creating persistent orphaned credentials that represent ongoing insider threat vectors.
Budget Waste and Duplicate Spending
- Organizations waste significant money on shadow IT. Employees purchase duplicate licenses for functionality that already exists in approved tools.
- Departments independently subscribe to similar services. Nobody tracks recurring subscriptions, leading to forgotten charges that continue indefinitely.
Optimization blind spots
Without visibility into actual tool usage, you can’t optimize software spending. You might be paying for 500 licenses of an approved tool while employees actually use a competing shadow IT solution, wasting both license costs.
Insider Threat Enablement
- Without security measures usually found in corporate networks, detecting insider threats in Shadow IT becomes nearly impossible.
- Employees with malicious intent who work from home use these kinds of unauthorized channels specifically because they allow them to circumvent data loss prevention (DLP) systems as well as monitoring and audit logs.
Data exfiltration made easy
- An employee planning to leave for a competitor can upload intellectual property to personal cloud storage with zero detection.
- Your SIEM, DLP, and monitoring tools see nothing because the shadow IT application is completely invisible to them.
Integration and Recovery Gaps
Shadow IT does not integrate with your backup systems, disaster recovery plans, or business continuity procedures—so if there is a problem, any data held in these unauthorized systems will be lost for good.
Incident response failure
- When you need to contain a threat, shadow IT creates operational nightmares. You can’t disable access to systems you don’t know about.
- You can’t restore data that was never backed up. You can’t investigate attacks against infrastructure outside your visibility.
How to Manage Shadow IT Risks
Implement Continuous Automated Asset Discovery
Traditional periodic scanning doesn’t work in cloud environments where resources spin up in minutes. Modern asset discovery uses agentless methods, API integrations, and continuous monitoring to maintain real-time visibility across your entire environment.
What effective discovery covers
- SaaS applications via Cloud Access Security Broker (CASB) integration
- Cloud infrastructure across AWS, Azure, GCP using native API polling
- Endpoints and devices through network protocol analysis
- Shadow AI workloads and unauthorized ML models
- Third-party integrations and connected services
Why continuous matters
Continuous discovery ensures you see that new shadow IT within minutes, not months. Platforms like Secure.com offer Digital Security Teammates that automatically classifies your assets, scores risk, and identifies shadow IT in real-time. It works across cloud, SaaS, and hybrid environments, reducing manual inventory work by 90% while providing complete asset visibility.
Establish Clear Shadow IT Policies with Fast Approval
Create explicit policies defining approved tools, prohibited categories, and consequences for policy violations. But equally important—make the approval process fast and transparent. Most shadow IT exists because employees can’t wait weeks for IT to evaluate new tools.
Policy framework
- Pre-approved tool catalog covering common use cases
- Fast-track approval (48-72 hours) for new tool requests
- Clear criteria for evaluation (security, compliance, cost)
- Self-service provisioning for approved applications
- Departmental tool budgets with autonomy within guardrails
Communication strategy
Punitive measures alone won’t solve shadow IT. Organizations must educate employees on security risks while providing approved alternatives that meet their productivity needs. Workers turn to this kind of technology because they need to get things done; if you stop them from using tools that haven’t been authorized but don’t offer any approved ones instead, then you’re not really fixing the problem.
Integrate Security Monitoring Across All Assets
Once discovered, shadow IT needs security coverage. Integrate all assets into your security monitoring stack—SIEM, EDR, vulnerability management, and access controls.
Unified visibility approach
- Centralized logging from all applications (approved and newly discovered)
- Identity governance extending to all SaaS applications
- Vulnerability scanning covering entire asset inventory
- Automated remediation workflows for common issues
- Risk-based prioritization using asset criticality and business context
Tools that help
Cloud Access Security Brokers (CASB), SaaS Management Platforms (SMP), and unified security platforms enabling single-pane-of-glass visibility. Secure.com consolidates asset discovery, risk scoring, and monitoring into one platform with 500+ integrations to existing security tools, eliminating tool sprawl while maintaining your current security investments. This enables security teams to manage SaaS risks without adding operational overhead or requiring additional headcount.
Improve IT Service Delivery Speed
The best shadow IT prevention is better IT service. When approved tools are easy to access, well-supported, and meet employee needs, shadow IT adoption drops dramatically.
Service improvements
- Self-service portal enabling easy access to frequently requested tools.
- Automated provisioning process– now taking minutes, not weeks.
- Providing user-friendly, approved alternatives to popular shadow IT.
- Establishing regular feedback loops with departments so we can understand their evolving tool needs.
- Running innovation pilots that allow us to evaluate new technologies safely.
Cultural shift
Moving away from “security says no” towards “security says yes, safely”. It’s not about trying to achieve zero shadow IT through prohibition alone– it’s better described as managing innovation in a way that ensures appropriate security controls are in place.
Why Does Shadow IT Happen? With Examples
Remote Work Acceleration
COVID-19 forced immediate remote work adoption. Employees needed collaboration tools immediately, couldn’t wait for IT approval, and adopted whatever worked. Video conferencing, project management, and file sharing services proliferated without central oversight.
Example
A marketing team began using Notion to track their projects because the tools they were given didn’t fit how they worked. Six months later, its database contained customer details, campaign plans, and supplier contracts—all stored outside the officially approved security perimeter.
Slow IT Approval Processes
When employees request IT tools, and it takes ages for approval, they find ways around the system. This happens because business units often feel they can move faster than slow-moving IT departments—creating constant pressure to adopt shadow solutions.
Example
Development team needed a CI/CD tool to meet project deadlines. After waiting three weeks for IT evaluation with no response, they deployed their own Jenkins instance on personal AWS accounts—creating unmanaged critical infrastructure outside the security perimeter. That instance became critical infrastructure, completely unmanaged and unpatched.
Inadequate Approved Tools
Sometimes approved tools genuinely don’t meet user needs. When IT mandates tools that are slow, unintuitive, or missing key features, employees adopt better alternatives independently.
Example
The sales team was supposed to use a clunky enterprise CRM but instead went with Airtable for their daily tasks. Lead data, customer relationships, and deal pipelines resided in the shadow IT system, while the official CRM contained only outdated information maintained solely for compliance purposes.
Department Autonomy and Budget
Departments with their own budgets often purchase tools directly without IT involvement, especially SaaS applications that don’t require technical installation or integration.
Example
Finance team subscribed to expense management SaaS using departmental credit card. The application integrated with their corporate bank accounts and contained years of financial data before security team discovered it during an unrelated audit.
Lack of Security Awareness
Many workers really don’t get why shadow IT causes problems. They perceive convenient productivity tools without recognizing the associated security and compliance risks. Free tier SaaS applications seem harmless until there are gigabytes of sensitive company data stored in them.
Example
An HR coordinator used her personal Gmail account to manage recruitment as “it was easier than Outlook.” Candidate CVs salary negotiations and background check details ended up over years, flowing through a private email account–breaking multiple employment laws in the process.
Shadow AI and ML Models
Shadow AI represents an emerging category of shadow IT—employees deploying AI tools and ML models without governance frameworks, data residency controls, or security review. Data scientists, developers, and business users now have access to powerful AI platforms capable of processing sensitive information—yet often deploy these tools without IT involvement or security review, creating significant data exposure risks.
Example
The product team used a free ChatGPT account to analyze customer feedback, inadvertently exfiltrating confidential customer data to an external AI service without data residency controls, privacy guarantees, or data processing agreements—creating potential GDPR and contractual violations.
FAQs
What percentage of IT assets are typically shadow IT?
Is shadow IT always malicious?
How does shadow IT differ from shadow AI?
Can shadow IT ever be beneficial?
How often should we scan for shadow IT?
What’s the first step to address shadow IT?
Conclusion
Employees adopt unauthorized tools to meet productivity needs that traditional IT approval processes cannot address quickly enough. The solution requires three elements: continuous automated discovery to eliminate blind spots, faster IT service delivery to reduce shadow IT adoption, and clear policies that enable secure innovation.
Contemporary platforms such as Secure.com spot all those hidden areas of shadow IT by continuously discovering assets without needing agents whether they’re in the cloud, SaaS, or hybrid setups. It provides real-time asset visibility while reducing manual inventory work by 90%.
Automated risk scoring, continuous security monitoring, and orchestrated response workflows provide the visibility and control needed to manage shadow IT effectively. Organizations face a clear choice: accept shadow IT as an unmanaged attack surface, or implement discovery and governance that transforms employee-driven innovation into secure, approved capabilities.
Start with complete visibility—you cannot protect what you cannot see.