Key Takeaways
- Most of the time lost in incident response happens between steps, not during them. The handoffs are where cases go quiet.
- There are 7 distinct handoff points: from the Security Information and Event Management (SIEM) system to the Endpoint Detection and Response (EDR) system, from EDR to the analyst, from the analyst to a Level 2 (L2) analyst, from the analyst to the engineer, from the engineer to the ticket, from the ticket to resolution, and from resolution to documentation. Each one is a chance for context to drop.
- Fixing one handoff does not fix the chain. The weakest link still determines how long the incident takes.
- Context loss forces analysts to reinvestigate what has already been done. That repeated work is avoidable and is one of the highest hidden costs in security operations.
- Good incident response keeps the investigation story intact from the first alert to the final resolution, so everyone who touches the case can act without having to start over.
Why Your Incident Response Keeps Stalling (And It Has Nothing to Do With Your Tools)
An alert fires. Your SIEM catches it. Then it moves to EDR. Then to an analyst. Then to a ticket. Somewhere in all that passing around, the clock keeps ticking, and the attacker keeps moving.
Most security teams focus on better detection or faster tools. But the real slowdown is not the investigation. It is everything in between.
Organizations take an average of 194 days to identify a breach and another 64 days to contain it. That is not a detection problem. A large chunk of that time is lost to handoffs.
Here is where your cases go quiet.
What a Handoff Actually Is (And Why It Matters)
A handoff is any moment when responsibility, data, or action moves from one tool or person to another.
In incident response, there are seven of them. Each one is a chance for context to drop, for priorities to shift, and for cases to sit idle while no one notices.
The 7 handoffs are:
- SIEM to EDR
- EDR to Analyst
- Analyst to L2 or Senior Analyst (L2 refers to Level 2 analyst)
- Analyst to Engineer
- Engineer to Ticketing System
- Ticket to Resolution
- Resolution to Documentation
Teams that struggle with MTTR almost always have a handoff problem, not a talent problem.
Where Cases Stall: All 7 Handoffs, Explained
Handoff 1: SIEM to EDR
Your SIEM collects logs from across the network and fires an alert. Then it hands that alert over to your EDR. The problem? SIEM and EDR speak different languages. SIEM focuses on aggregating and correlating data from multiple sources, while EDR focuses on the endpoint level with a more focused, granular approach. When an alert crosses between them, the context built in one system rarely survives the trip to the other.
The analyst who eventually receives it has to figure out what already happened. That costs time.
Handoff 2: EDR to Analyst
The alert lands in an analyst’s queue. But it shows up stripped of the investigation thread that was built upstream. Without proper filtering, security teams must sift through irrelevant or low-priority alerts, leading to alert fatigue. Alert fatigue occurs when analysts become overwhelmed by the sheer volume of alerts, causing them to miss critical incidents or respond more slowly than necessary.
The analyst is not starting from the alert. They are starting from scratch.
Handoff 3: Analyst to L2 or Senior Analyst
Someone decides this case needs senior eyes. They escalate. The note they write is thin. Maybe three lines. The L2 analyst who receives it has to re-read the case, re-investigate what was already checked, and form their own view before doing anything useful.
This is repeated work. It is also one of the most common bottlenecks inside SOC teams.
Handoff 4: Analyst to Engineer
The case needs a fix at the infrastructure level. The analyst sends it to an engineer. But the engineer does not have the full story of the investigation. They have a ticket summary and a severity tag. Now they have to make decisions with an incomplete context.
Engineers prioritize based on what they know. If they know little, the case waits.
Handoff 5: Engineer to Ticketing System
The case becomes a ticket. Generic title. Vague description. Assigned to a queue where it will compete with every other open item. Tight integration among detection and response platforms, ticketing systems, and automation playbooks streamlines handoffs, reduces manual effort, and increases the consistency and speed of incident handling. Without that integration, tickets age quietly while no one flags them.
Handoff 6: Ticket to Resolution
The ticket gets picked up. Or it does not. Even when someone acts on it, they often have to chase down the original analyst for context that should have been in the ticket in the first place.
A resolution that should take an hour stretches into a day.
Handoff 7: Resolution to Documentation
The incident is closed. Lessons learned get skipped. Nobody writes down what happened, what worked, or what to do differently. The next similar incident starts from zero.
This handoff failure does not hurt today. It hurts in three months when the same type of attack comes back, and your team has no memory of it.
Why Fixing One Handoff Is Not Enough
Teams may fix one gap and consider their work done, perhaps faster SIEM rules, better ticket templates, or a new EDR integration.
It does not hold.
Incident response is a chain. Fix one link, and the weak ones downstream still break. Most delays cluster in three areas: analyst triage backlogs, manual investigation steps, and remediation action approval processes. Those three areas span multiple handoffs. You cannot fix them by improving just one of them.
There is also a compounding cost. Every handoff adds minutes, which quickly become hours. In cybersecurity, the longer an attacker dwells, the greater the business risk. Ransomware attackers can move within days of gaining access. If your response chain takes longer, you may lose the opportunity to contain the attack.
The data backs this up. The average time to identify and contain a breach fell to 241 days in 2025, a nine-year low. Progress, yes. But still more than half a year. Much of that time is spent waiting between steps rather than working on them.
What Good Incident Response Actually Looks Like
The goal is not to remove humans from the process. It is to remove the friction that slows humans down.
A Shared Investigation Thread
When SIEM, EDR, and case management are connected through a common layer, the analyst does not have to rebuild context. The investigation story follows the alert from first detection all the way through to resolution. Everyone who touches the case sees the same timeline.
Escalations That Carry Context
A good escalation is not just reassigning a ticket. It is sending the full investigation summary, the enriched evidence, and a clear statement of what decision needs to be made next. The receiving analyst should be able to act in minutes, not hours.
Tickets That Mean Something
Tickets should arrive with enough context for an engineer to make a real decision without a follow-up call. That means attaching the timeline, the impacted assets, the threat intelligence context, and the recommended action. Not just a severity label.
Documentation Built Into the Workflow
Post-incident documentation should not be a separate task. It should be captured automatically as the case moves through each step. By the time the incident closes, the record is already written.
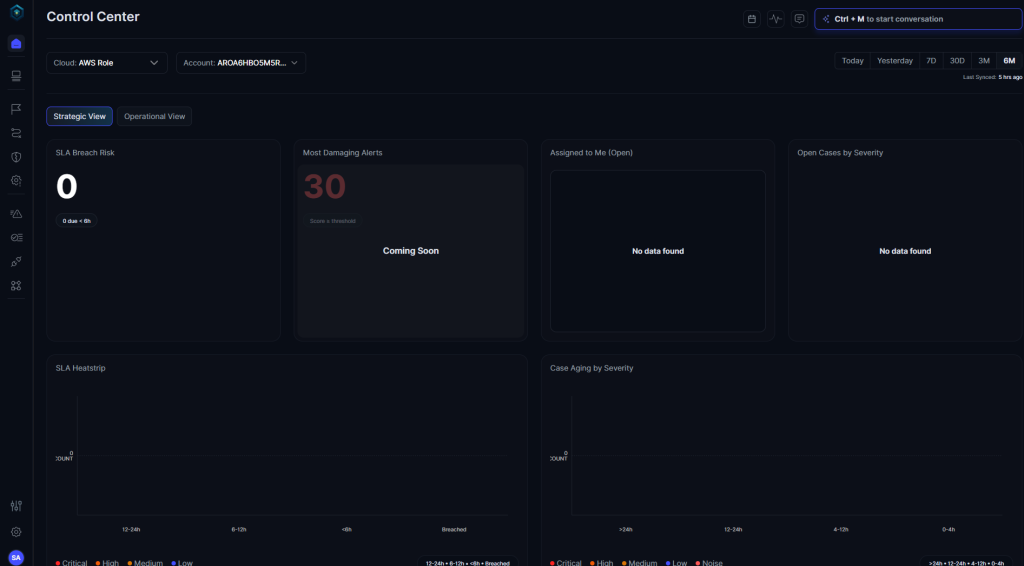
How Secure.com Helps You Close the Gaps
Most tools improve individual handoffs. Secure.com considers the entire response chain.
Secure.com is built around the idea that context should never have to be rebuilt. Digital Security Teammate normalizes data from SIEMs, EDRs, and threat feeds into a single continuous investigation thread so that each person who touches a case gets the full picture, not a summary of a summary.
Here is what that looks like in practice:
- Alerts from SIEM and EDR are normalized into a unified view, eliminating context loss across tools.
- Escalations automatically include the full investigation summary, evidence, and the recommended next step.
- Engineers receive decision-ready cases, not vague ticket descriptions.
- Every action taken during an investigation is logged with a full audit trail, building the post-incident record as it happens.
- Playbooks run automatically for common scenarios, so analysts spend time on judgment calls rather than repetitive steps.
The result is a response chain where context travels with the case. Not just detection, not just containment. The full loop from first alert to final documentation, without rebuilding from scratch at every step.
Conclusion
Incident response is only as fast as its slowest handoff. Most teams spend time improving how they detect or investigate threats. But if the transfers between those stages are broken, those improvements will not show up in response times. Map your all seven handoffs. Find where context drops. That is where the real work is.
FAQs
What is a handoff in incident response?
A handoff is any point where an alert, case, or responsibility moves from one tool or person to another. Each handoff is a chance for context to disappear and delays to stack up.
Why do incidents stall between SIEM and EDR?
SIEM and EDR tools collect different types of data and do not share a common case format. When an alert moves from one system to another, the enrichment and context built in the first system often do not follow.
How does analyst escalation cause slowdowns?
When a case is escalated with a thin note, the receiving analyst has to reinvestigate what has already been done. Repeated work is one of the most common causes of slower resolution times inside SOC teams.
What makes a ticket delay different from a resolution delay?
A ticket delay happens when a case sits in a queue without clear ownership. A resolution delay occurs when the engineer working on the ticket lacks sufficient information to act confidently. Both are handoff problems, just at different stages.
Can AI actually fix handoff problems?
AI helps when it is built into the investigation workflow, not bolted on afterward. The right approach normalizes data across tools, carries context through escalations automatically, and surfaces the right information to the right person at each stage. That removes the rebuilding step that causes most handoff delays.