TL;DR
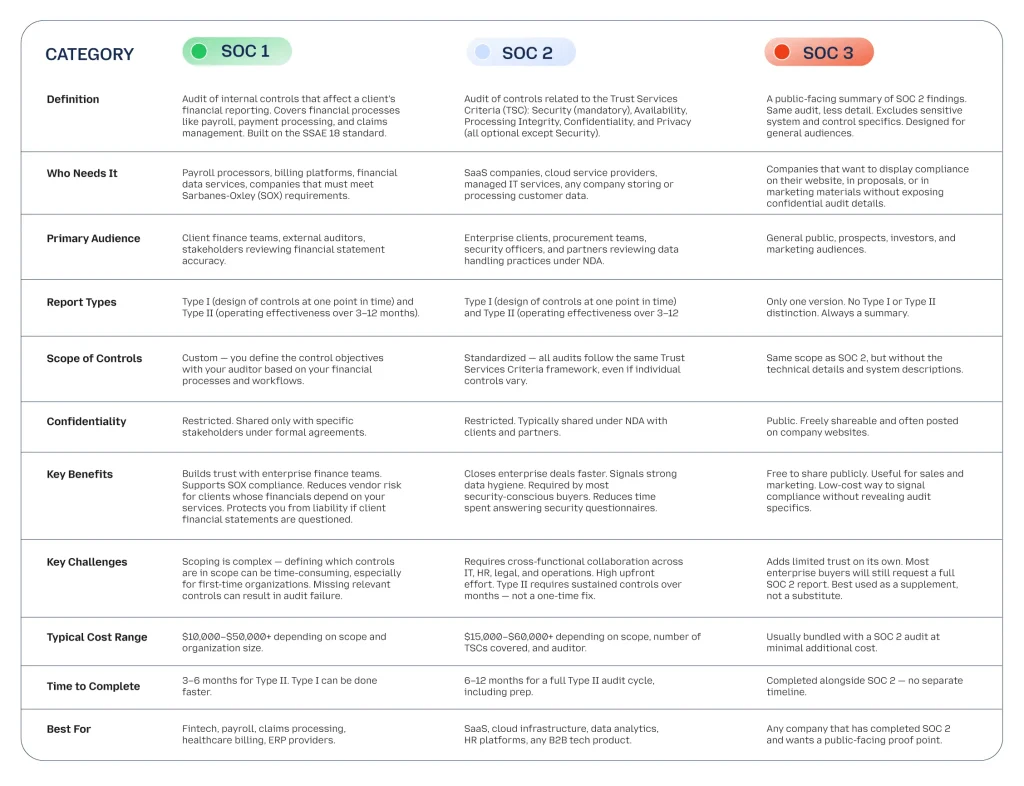
- SOC 1 = financial controls.
- SOC2 = data security controls.
- SOC 3 = public-facing summary of SOC2.
- The numbers don’t mean levels — you don’t need SOC 1 before SOC 2.
- Most tech companies need SOC2.
- If your product touches client financials, you may also need SOC 1.
- SOC 3 is optional — it’s just a marketing-safe version of SOC2.
Key Takeaways
- SOC reports are issued by independent CPA firms under the framework of American Institute of Certified Public Accountants (AICPA).
- SOC 1 and SOC2 both come in Type I (point-in-time) and Type II (over time) versions.
- Enterprise buyers are demanding SOC compliance more than ever — SOC2 report issuances grew 23% in 2023, according to KPMG.
- The right SOC report can shorten your sales cycle with security-focused buyers.
- You can hold multiple SOC reports at the same time if your business needs it.
Introduction
Over 60% of enterprise procurement teams require a SOC report before signing a vendor contract. If you’re in SaaS, fintech, or any B2B service, you’ve probably been asked for one — and had no idea where to start.
SOC 1, SOC2, and SOC 3 sound like a progression. They’re not. Each one solves a different problem for a different audience. Choosing the wrong report can waste months of audit preparation and still fail to meet your prospects’ requirements.
This guide breaks down each report in plain terms so you know exactly what you need — and why.
What Is a SOC Report?
SOC stands for Service Organization Controls. These are independent audit reports created under standards set by American Institute of Certified Public Accountants (AICPA).
A SOC report proves — through a third-party CPA audit — that your company has the right controls in place. Whether those controls protect financial data, customer data, or system availability depends on which report you pursue.
Service organizations (think cloud providers, payroll processors, SaaS companies) use SOC reports to build trust with clients who don’t have direct visibility into their internal systems. Without one, enterprise buyers have no way to verify your claims about security or compliance.
There are three main types: SOC 1, SOC2, and SOC 3. Two additional types — SOC for Cybersecurity and SOC for Supply Chain — exist but are far less common.
What’s the Difference Between SOC 1, SOC 2, and SOC 3?
Think of the three reports this way: SOC 1 is for your client’s finance team. SOC2 is for their security and IT team. SOC 3 is for everyone else.
Here’s a full breakdown:
Conclusion
SOC 1, SOC 2, and SOC 3 are not competing options — they serve completely different needs.
If your product touches a client’s financial reporting, get SOC 1. If you’re in SaaS or cloud services and want enterprise deals, get SOC 2 Type II. If you’ve already completed SOC 2 and want something to share publicly, add SOC 3 while you’re at it.
Most growing tech companies will eventually need SOC2. The question isn’t if — it’s when. Starting early gives you a head start before an enterprise deal requires it on a tight deadline—often 30 days or less.
Not sure which report fits your business? Talk to a compliance advisor to map the right path before committing to an audit.