The last week of November 2025 has delivered a sobering reminder that modern cyber threats are becoming more automated, interconnected, and destructive.
We observed self-replicating worms compromising developer environments and state-sponsored malware infiltrating enterprise update systems. This week’s incidents reveal an alarming evolution in attacker sophistication and scale.
For CISOs, CTOs, and security teams, these five incidents demand immediate attention – not just for their technical severity, but for what they signal about the changing nature of cyber risk.
Top Attacks and Breaches
1. Sha1-Hulud 2.0: The Self-Replicating NPM Nightmare
During November 21-24, a sophisticated worm compromised over 800 NPM packages with 132 million weekly downloads, including libraries from Zapier, ENS Domains, PostHog, and Postman. Dubbed “Sha1-Hulud: The Second Coming,” this worm launched a supply chain attack. Unlike typical supply chain attacks however, this malware operated with unprecedented automation and aggression.
How does it work?
The worm activates during the npm preinstall lifecycle phase. It harvests credentials from developer machines and CI/CD pipelines, targeting npm tokens, GitHub keys, and cloud credentials (AWS, Azure, GCP), then exfiltrates them to public GitHub repositories. Over 25,000 repositories have been created, exposing 11,858 unique secrets with 2,298 remaining valid as of November 24.
This worm uses stolen npm tokens to backdoor up to 100 additional packages per compromised developer through self-replication. It establishes persistence via GitHub Actions workflows, turning infected systems into attacker-controlled runners.
If credential theft fails, the malware attempts to destroy the victim’s entire home directory—a punitive escalation from data theft to catastrophic sabotage. The attack has even spread to Java’s Maven ecosystem, demonstrating cross-platform propagation.
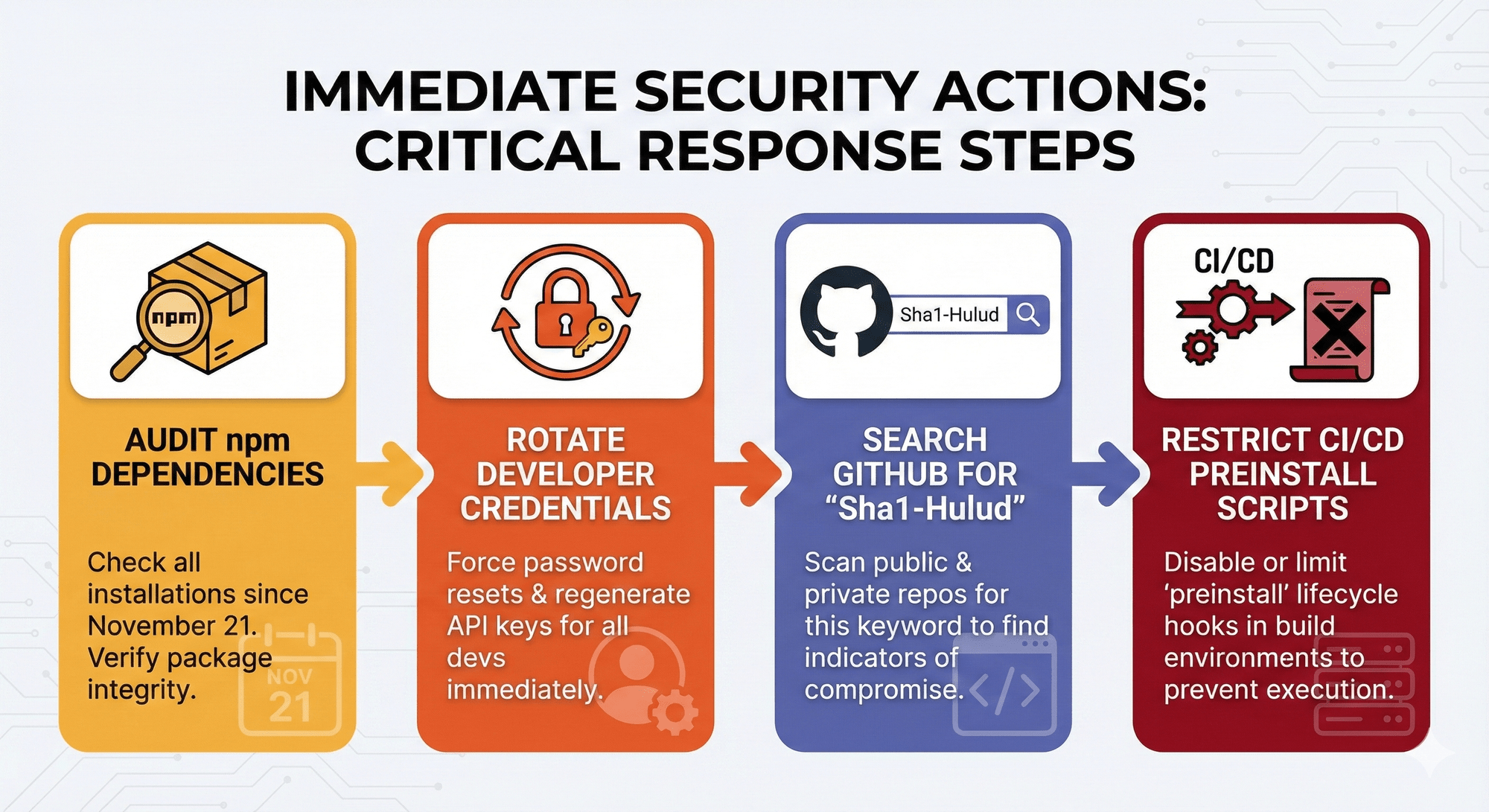
Immediate actions: Audit all npm dependencies installed since November 21. Rotate all developer credentials. Search GitHub for “Sha1-Hulud” repositories. Restrict preinstall lifecycle scripts in CI/CD environments.
2. Chrome Zero-Day Marks Seventh Browser Exploit of 2025
Google patched CVE-2025-13223 on November 18—a type confusion vulnerability in Chrome’s V8 JavaScript engine actively exploited in the wild. This marks the seventh Chrome zero-day weaponized this year, an unprecedented exploitation pace that underscores browsers as primary attack surfaces.
Discovered by Google’s Threat Analysis Group (TAG), which specializes in tracking government-sponsored spyware and nation-state operations, the vulnerability allows remote code execution via malicious webpages. TAG’s involvement strongly indicates exploitation by advanced threat actors targeting journalists, dissidents, and opposition figures.
The V8 engine vulnerabilities observed throughout 2025 reflect attackers’ systematic focus on JavaScript execution paths. With Chrome commanding over 65% of the browser market, these zero-days provide access to millions of potential victims.
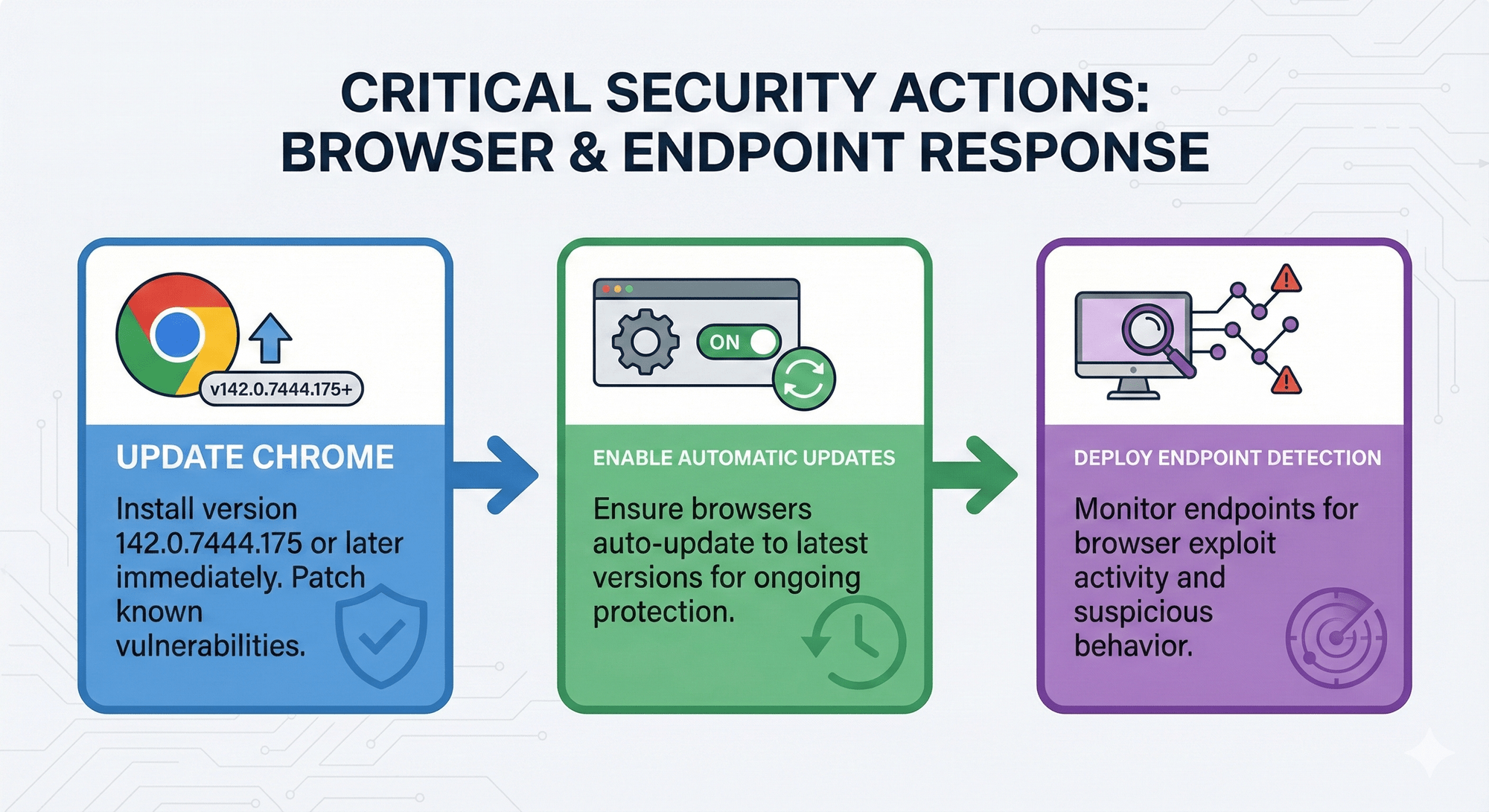
Critical actions: Update Chrome to version 142.0.7444.175 or later. Enable automatic updates. Deploy endpoint detection for browser exploit activity.
3. Qilin Ransomware’s MSP Attack on South Korean Finance
A sophisticated supply chain attack compromised 28 South Korean financial firms, primarily asset management companies – through a single MSP breach. The Qilin ransomware group infiltrated GJTec, a domestic IT service provider, gaining simultaneous access to multiple client networks and stealing over 1 million files (2TB of data) in its “Korean Leaks” campaign.
What elevates this incident beyond typical ransomware is potential North Korean state involvement. Moonstone Sleet, a North Korean APT group, is operating as a Qilin affiliate—demonstrating the convergence of nation-state actors using criminal RaaS platforms for both financial gain and geopolitical objectives.
The attackers employed propaganda-style messaging, framing data exfiltration as exposing systemic corruption and threatening to trigger national market crises. This blend of financially motivated cybercrime with state-sponsored operations complicates attribution and response.
Qilin dominated October 2025, claiming 180+ victims and accounting for 29% of all global ransomware attacks. The Korean campaign demonstrates how compromising a single vendor with privileged access enables “cluster victim” targeting at scale.
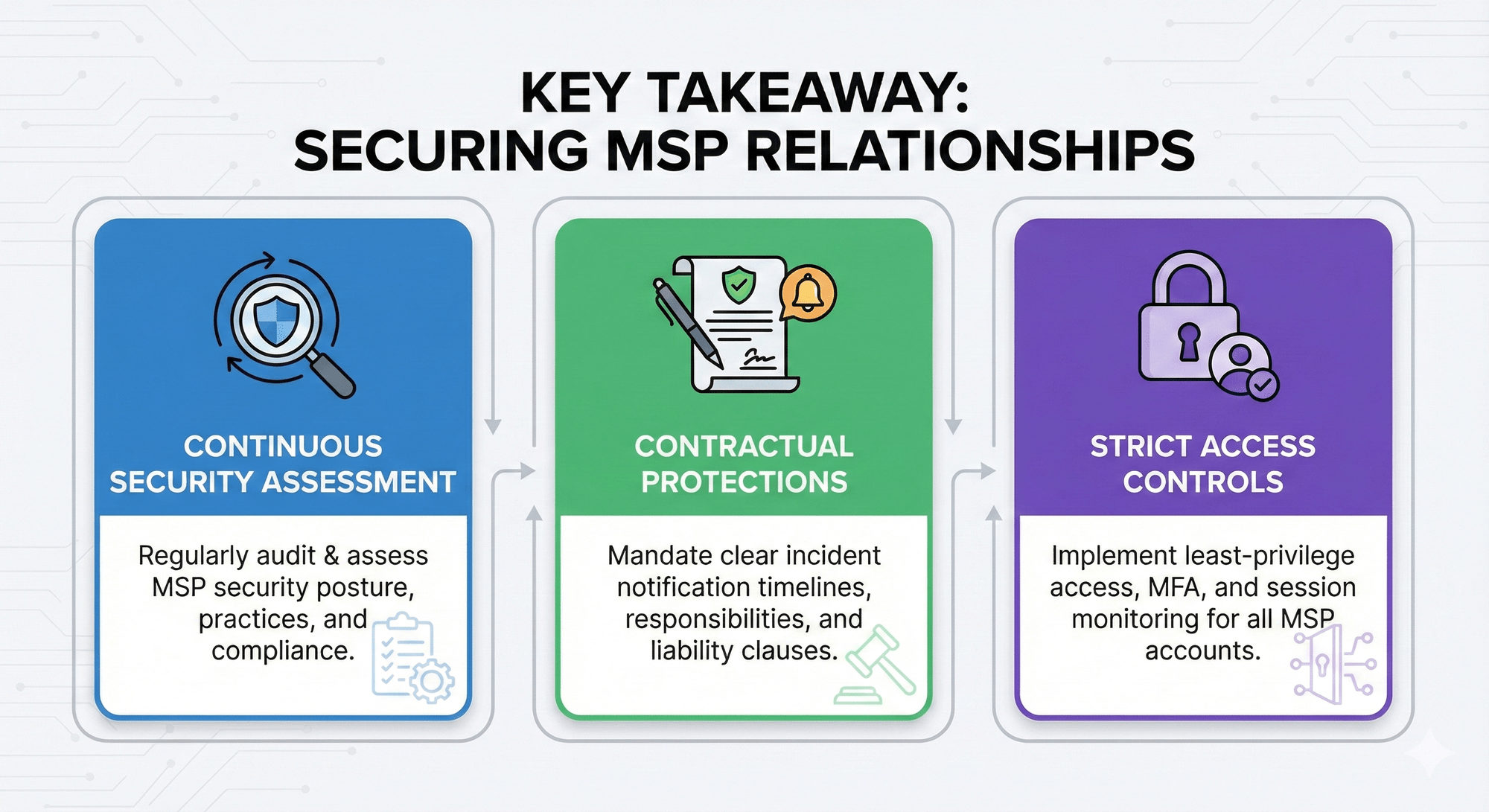
Key takeaway: MSP relationships require continuous security assessment, contractual protections for incident notification, and strict access controls following least-privilege principles.
4. Chinese APTs Target WSUS Vulnerability to Deploy ShadowPad Malware
Chinese state-sponsored groups are exploiting a previously patched vulnerability to deploy ShadowPad malware across enterprise networks. They exploit a critical WSUS vulnerability to achieve unauthenticated remote code execution with SYSTEM privileges on Windows Server Update Services infrastructure.
Although Microsoft patched the vulnerability in October, threat actors weaponized it within hours of the public proof-of-concept release. The CISA has mandated federal agencies to deploy a patch within 48 hours, reflecting the severity of compromising enterprise update infrastructure.
Researchers have documented multi-stage attacks where adversaries first establish reverse shells using PowerCat, then deploy ShadowPad via legitimate Windows utilities (curl, certutil) to evade detection. ShadowPad, described as “a masterpiece of privately sold malware in Chinese espionage,” operates through DLL side-loading and maintains persistence via scheduled tasks, registry modifications, and process injection.
The strategic impact cannot be overstated: WSUS serves as the nerve center for Windows patching. Attackers who gain control of this infrastructure can deploy malicious updates disguised as legitimate patches, achieving enterprise-wide compromise through trusted mechanisms—reminiscent of the SolarWinds supply chain attack.
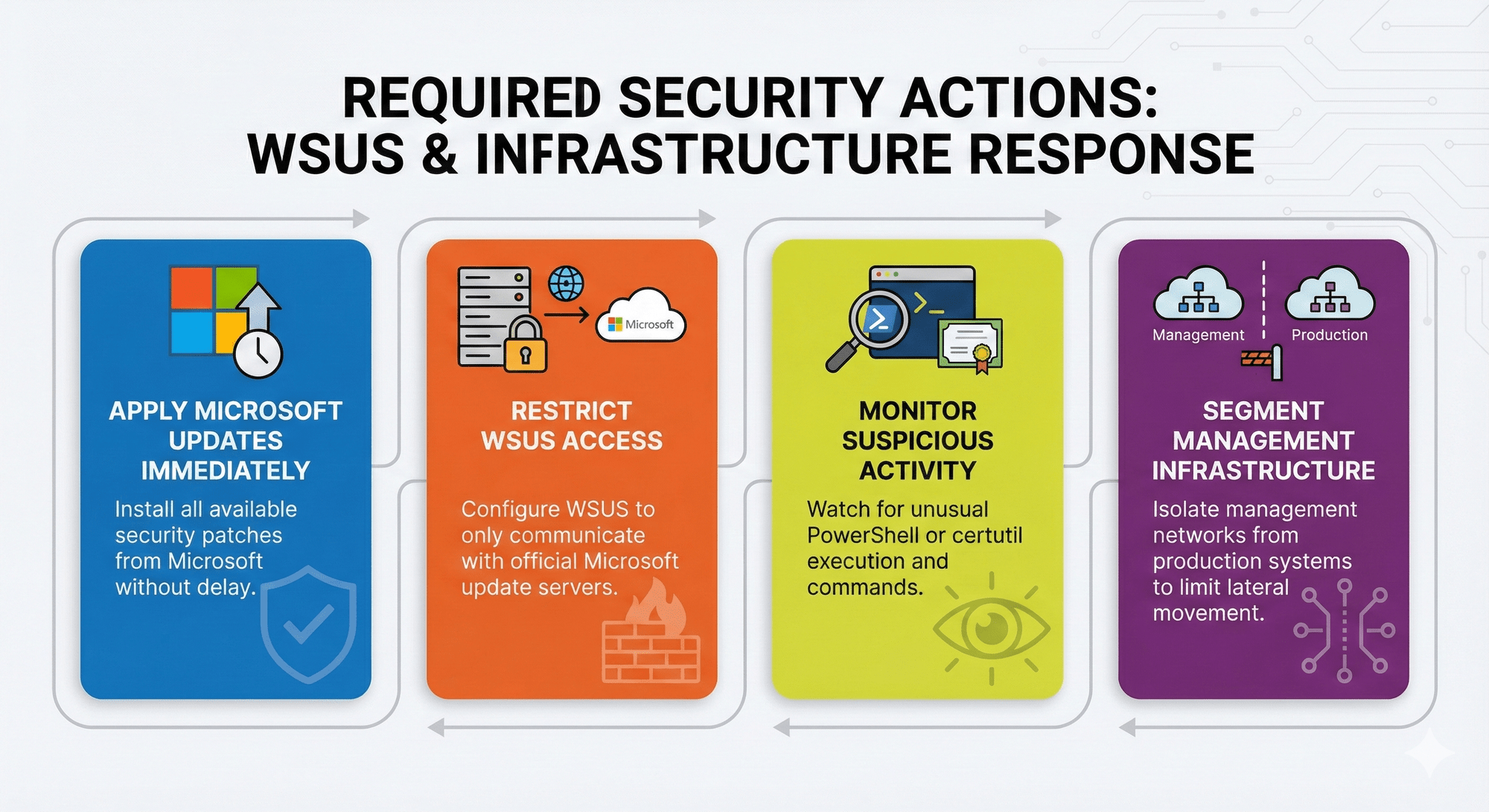
Required actions: Organizations should apply Microsoft updates immediately. There is also a need to restrict WSUS access to Microsoft servers only, monitor for suspicious PowerShell/certutil activity, and segment management infrastructure from production networks.
5. Red Hat GitLab Breach Exposes Customer Credentials
Red Hat confirmed that attackers stole 570GB from 28,000+ internal repositories in its consulting team’s GitLab instance, compromising approximately 800 Customer Engagement Reports containing infrastructure details, configurations, and credentials for enterprise clients.
The breach, disclosed by the Crimson Collective extortion group, highlights concentrated risk in consulting relationships. While Red Hat believes its core software supply chain remained separate, consulting teams necessarily maintain privileged customer access—creating high-value targets for adversaries seeking multiple downstream victims through a single compromise.
These exposed Customer Engagement Reports gave attackers access to detailed reconnaissance: security architectures, monitoring capabilities, network segmentation, and access credentials. If customers fail to rotate compromised credentials promptly, adversaries can pivot directly into enterprise environments using legitimate access.
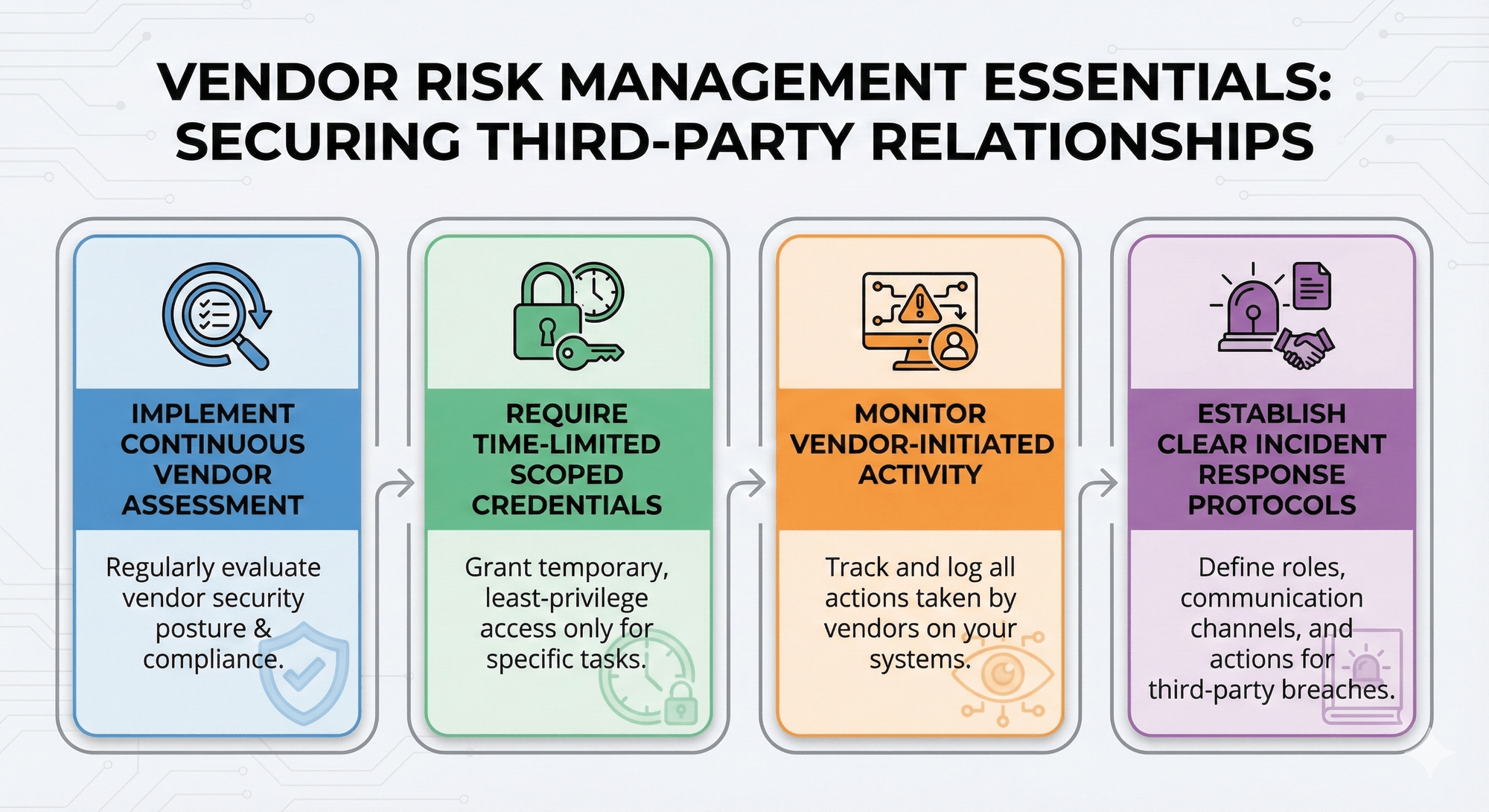
Vendor risk management essentials:
Implement continuous vendor assessment. Require time-limited scoped credentials, monitoring for vendor-initiated activity, and clear incident response protocols for third-party breaches.
Recommendations
Critical Actions
Immediate (Next 24-48 Hours):
NPM Supply Chain
- Audit all npm dependencies installed since November 21, 2025
- Search GitHub for repositories matching “Sha1-Hulud: The Second Coming”
- Rotate all npm tokens, GitHub PATs, SSH keys, and AWS/Azure/GCP credentials
- Review all .github/workflows/ directories for unauthorized discussion.yaml files
- Check self-hosted GitHub runners for names containing “SHA1HULUD”
Browser Security
- Update Chrome to version 142.0.7444.175 or later across all endpoints
- Enable automatic browser updates organization-wide
- Deploy endpoint detection rules for browser exploit activity
Windows Infrastructure
- Apply Microsoft CVE-2025-59287 patch to all WSUS servers immediately
- Restrict WSUS access to Microsoft Update servers only
- Analyze logs for certutil and curl execution patterns
- Search for scheduled tasks or services named “Q-X64”
Vendor & Third-Party Access
- Inventory all MSP and consulting firm access points
- Rotate credentials, especially those associated with Red Hat or recent vendor engagements
- Review access logs for anomalous vendor activity dating back to September 2025
Short-Term (Next 7-14 Days):
- Implement npm lifecycle script restrictions in CI/CD pipelines
- Conduct phased vendor security assessments focusing on access controls and incident response protocols
- Implement automated dependency scanning for malicious packages
- Segment management infrastructure from production systems
- Enable phishing-resistant multi-factor authentication for all developer and CI/CD accounts
Strategic (Next 30-90 Days):
- Implement comprehensive Software Bill of Materials (SBOM) tracking
- Create and implement playbooks for vendor breach incident response
- Implement zero-trust architecture for third-party access
- Implement continuous vendor risk monitoring programs
- Deploy deception technology in critical infrastructure environments
- Conduct regular tabletop exercises that double as supply chain compromise scenarios
Policy & Governance:
- Update vendor contracts to require 24-hour breach notification
- Require security attestations from service providers as standard practice
- Implement least-privilege access policies for external vendors
- Require time-limited, scoped credentials for all consulting engagements
- Separate development, staging, and production dependency sources
Monitoring & Detection:
- Enable alerts for new GitHub repositories under organizational accounts
- Monitor unusual outbound connections from developer workstations
- Deploy EDR with behavioral detection for living-off-the-land techniques
- Implement WSUS integrity monitoring and update signing verification
- Establish baseline behavior profiles for npm package installation patterns
Reactive patching is no longer sufficient – today’s organizations must implement continuous validation, assume breach, and architect systems for rapid detection and containment.
Intelligence Summary
We’re observing fundamental shifts in how adversaries operate. Automation enables attacks that scale exponentially without human intervention. State actors are increasingly leveraging criminal ecosystems for operational cover and financial sustainability.
The path forward for security leaders is clear: match adversary automation with defensive automation through continuous dependency monitoring, rapid patch deployment, real-time threat intelligence integration, and comprehensive vendor risk management. The modern attack surface extends far beyond organizational perimeters—encompassing every developer dependency, vendor relationship, and third-party integration.
The threats documented this week aren’t anomalies—they’re the new baseline.
Adaptation isn’t optional.
Stay ahead of emerging threats.